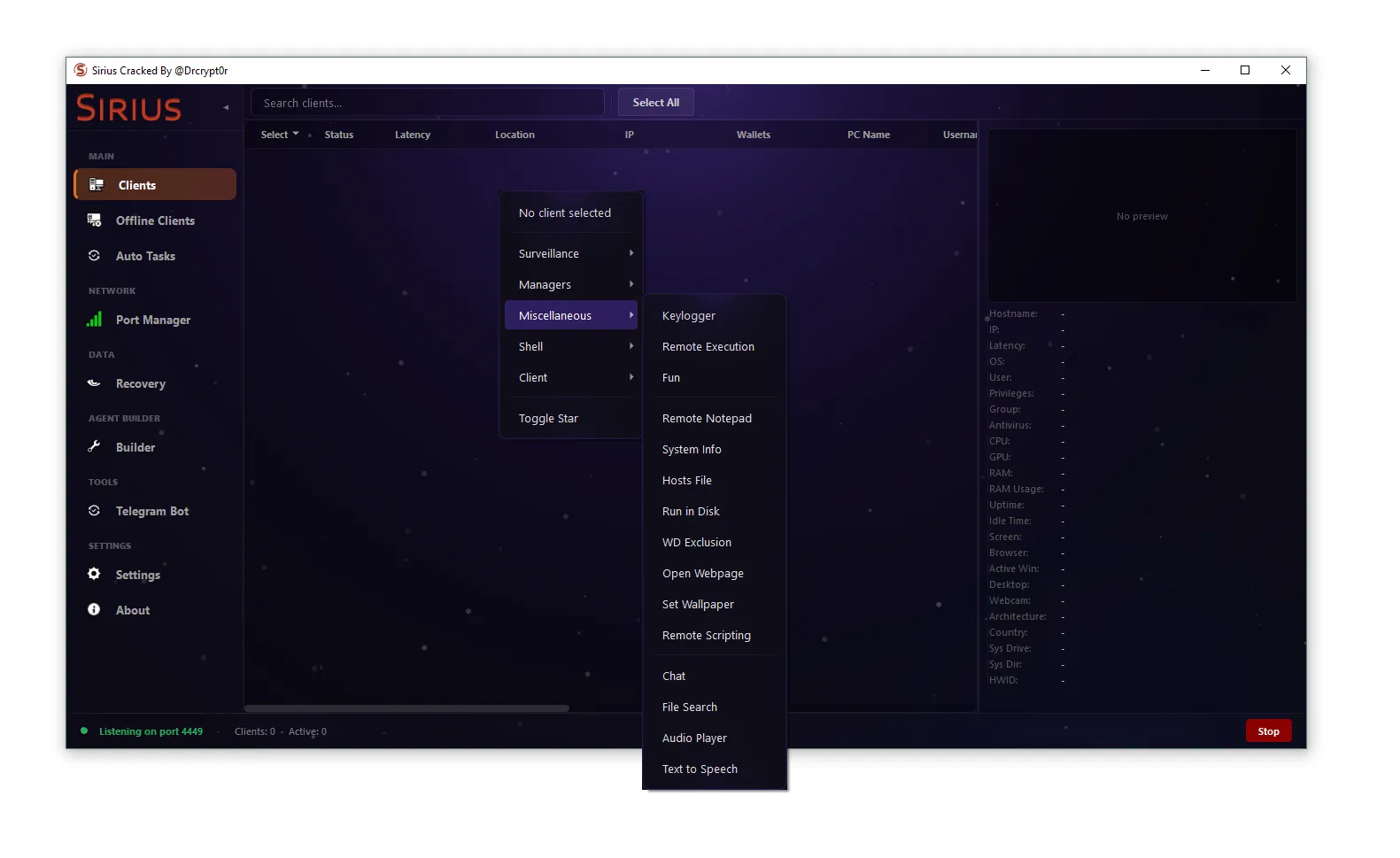
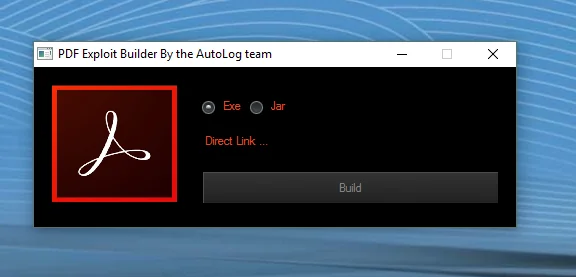
📄 PDF Exploit Builder Cracked 2026 – Complete Guide
🔎 Introduction
PDF Exploit Builder Cracked 2026 is a powerful toolkit designed for creating PDF files with embedded scripts or exploit payloads. These specially crafted PDFs can target vulnerabilities in PDF readers or use social engineering to perform automated actions when opened.
While commonly discussed in cybersecurity contexts, these tools are primarily used for penetration testing, exploit development, and malware research. Misuse of these tools can lead to phishing attacks, malware distribution, and unauthorized access, so they must be handled responsibly.
⚙️ What is PDF Exploit Builder Cracked 2026?
A PDF Exploit Builder is software that generates malicious or research-oriented PDF files by embedding code, scripts, or exploit payloads.
PDF files are versatile containers that can include:
- 📜 Embedded JavaScript
- 🎵 Multimedia objects
- 🔗 External links
- 📝 Form fields
- ⚡ Automatic actions on file open
These features make PDFs a potential attack vector if vulnerabilities exist in the reader software. Exploit builder tools automate the process of embedding these elements efficiently.
🧠 How PDF Exploit Builder Cracked 2026 Techniques Work
Malicious PDF attacks often rely on one or more of these techniques:
1️⃣ Embedded JavaScript
PDF files can contain JavaScript code that executes automatically. Attackers may exploit vulnerabilities in PDF readers to trigger unauthorized actions.
2️⃣ Exploiting Reader Vulnerabilities
Some attacks target specific vulnerabilities in PDF reader software, which can lead to remote code execution when a malicious PDF is opened.
3️⃣ Social Engineering
Attackers may trick users into executing actions by embedding:
- ⚠ Fake “secure document” prompts
- 🔒 Login forms within PDFs
- 🖱 Clickable buttons redirecting to malicious websites
Social engineering combined with PDF features increases the chance of successful attacks.
🧩 Features of PDF Exploit Builder Tools
Typical PDF exploit builders include features such as:
- 📂 Custom payload embedding
- 🔗 Malicious URL injection
- 🧾 Template-based PDF creation
- 🛡 Obfuscation to evade detection
- ⚡ Automatic exploit generation
- 📦 Payload delivery configuration
These features simplify the creation of testing PDFs or research-oriented exploits for cybersecurity purposes.
🧪 Legitimate Uses in Cybersecurity
In controlled environments, PDF exploit builders are used for:
- 🕵️♂️ Penetration testing
- 🧪 Malware analysis
- 🛠 Exploit development
- 🎓 Security training labs
- 🖥 Testing antivirus detection capabilities
Security researchers leverage these tools to evaluate systems without harming real users.
⚠️ Risks of Malicious PDFs
PDF-based attacks are common because PDFs are widely trusted. Opening malicious PDFs can lead to:
- 💻 Malware installation
- 🛡 Credential theft
- 🌐 Redirects to phishing pages
- ⚡ Exploitation of software vulnerabilities
Awareness of these risks is essential for both individuals and organizations.
🛡 How to Protect Against PDF Exploits
To reduce risks from malicious PDFs:
✔ Keep PDF readers updated
✔ Disable JavaScript in PDF viewers
✔ Avoid opening PDFs from unknown sources
✔ Scan attachments with antivirus software
✔ Use sandbox tools for testing suspicious files
Organizations also deploy email security systems to prevent delivery of harmful PDFs.
Download PDF Exploit Builder Cracked 2026
📌 Conclusion
PDF Exploit Builder Cracked 2026 is a tool for creating advanced PDFs with embedded exploit techniques. While these tools have legitimate uses in cybersecurity research, they are often misused in phishing and malware campaigns. Understanding their mechanisms allows better protection against document-based attacks.