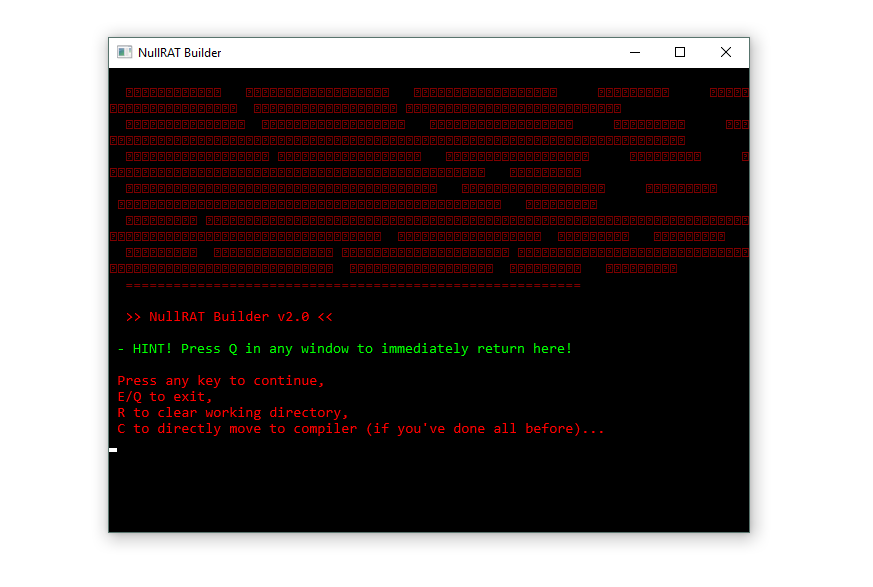
🧠 Introduction to NullRAT 2026
The cybersecurity landscape continues to evolve as attackers develop increasingly sophisticated malware frameworks. One of the threats gaining attention in malware research communities is NullRAT 2026, a Python-based Remote Access Trojan designed to provide attackers with remote control over infected systems.
Remote Access Trojans are particularly dangerous because they allow cybercriminals to silently monitor users, steal credentials, and execute commands remotely without the victim noticing. The modular design of NullRAT 2026 malware makes it adaptable for different cyber-attack scenarios.
Understanding the behavior and capabilities of NullRAT 2026 is essential for security researchers, IT professionals, and organizations looking to strengthen their cybersecurity defenses.
🦠 What is a Remote Access Trojan (RAT)?
A Remote Access Trojan (RAT) is a type of malware that enables attackers to control a compromised device remotely.
Unlike traditional viruses that simply damage systems, RAT malware focuses on long-term system access and surveillance.
🎯 Common RAT Capabilities
🔹 Remote command execution
🔹 File management and manipulation
🔹 System monitoring and surveillance
🔹 Keylogging and credential theft
🔹 Screenshot and activity capture
🔹 Network communication with attacker servers
These capabilities allow attackers to gain complete control over compromised systems.
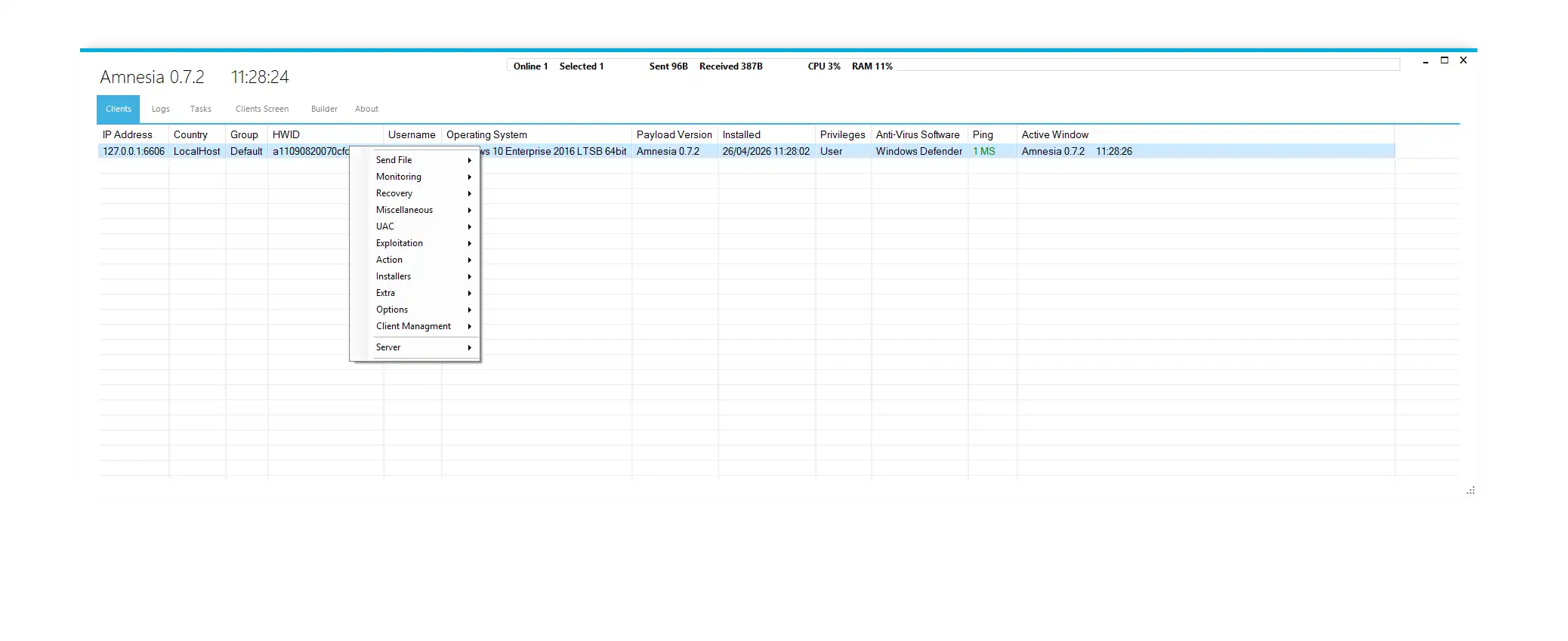
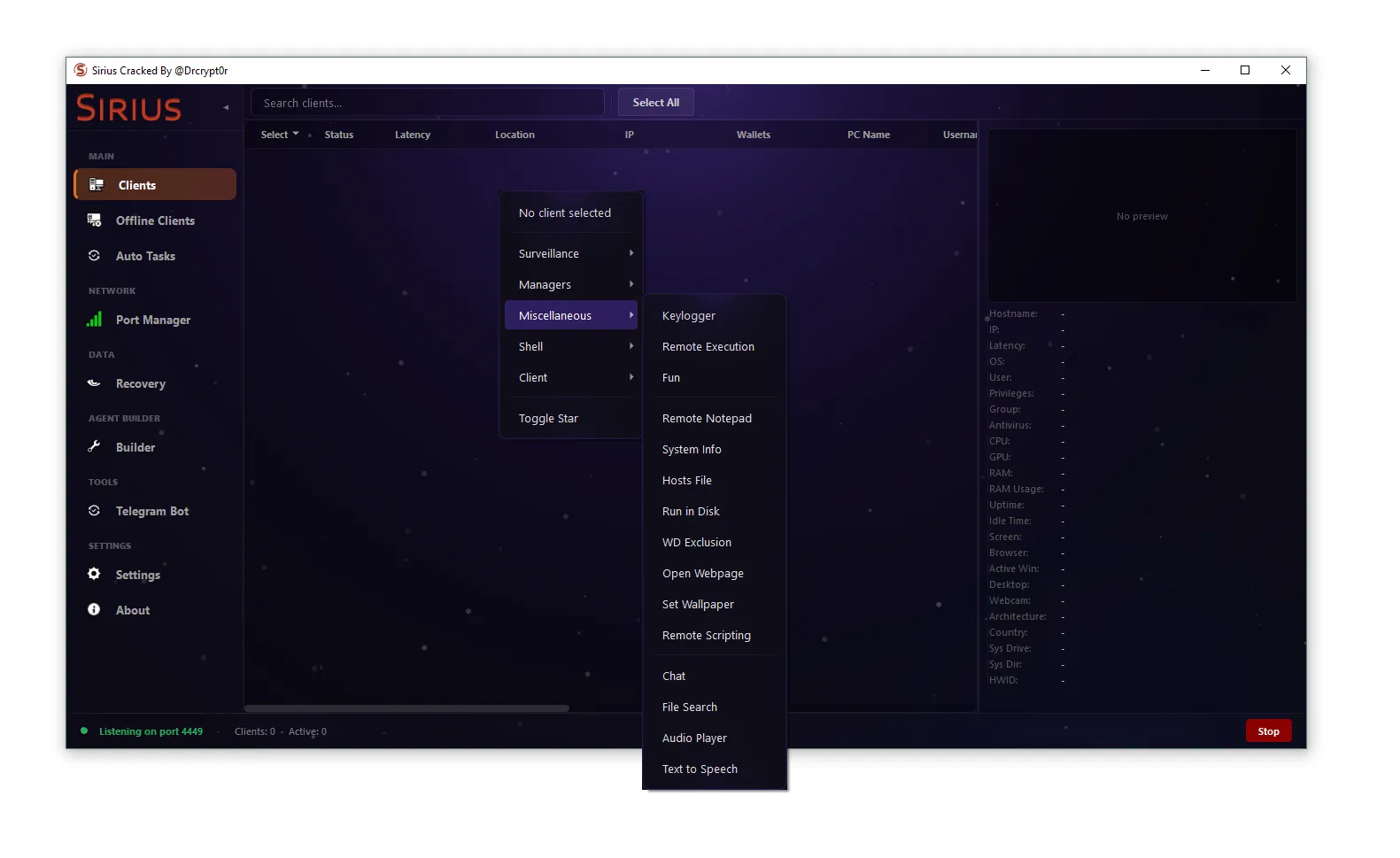
🔍 Overview of NullRAT 2026 Malware
NullRAT 2026 is a malware framework designed to establish remote connections between infected systems and attacker-controlled infrastructure.
📌 Core Characteristics
🧩 Python-based malware architecture
🧩 Remote command execution capabilities
🧩 System surveillance and monitoring features
🧩 Data theft and credential harvesting functionality
🧩 Modular structure allowing feature expansion
Because the malware is written in Python, it can be easily modified and adapted by attackers for different malicious campaigns.
⚙️ Key Features of NullRAT 2026
Modern RAT malware typically includes several dangerous capabilities.
🖥 Remote System Control
One of the primary features of NullRAT 2026 is remote system administration.
🔧 Remote Control Functions
⚙️ Execute commands on the victim machine
⚙️ Run scripts remotely
⚙️ Manage files and directories
⚙️ Control system processes
This allows attackers to operate compromised devices from anywhere.
📸 Surveillance and Monitoring
RAT malware is frequently used for digital surveillance.
👁 Monitoring Capabilities
📸 Screenshot capturing
⌨️ Keylogging activity tracking
📋 Clipboard monitoring
🖥 System information gathering
These features enable attackers to monitor user behavior and collect sensitive data.
🔐 Credential and Data Theft
Stealing sensitive information is often the primary objective of malware campaigns.
💳 Targeted Information
🔑 Browser saved passwords
📧 Email login credentials
💬 Messaging platform accounts
💰 Cryptocurrency wallet information
📁 Personal and corporate documents
Once stolen, this information may be used for identity theft or financial fraud.
🧬 Technical Architecture of NullRAT 2026
Modern malware frameworks are often built using modular architecture.
🧩 Core Components
🖥 Client payload running on victim system
📡 Command and control server communication module
⚙️ Execution engine handling commands
📂 Data collection module gathering sensitive information
This architecture enables attackers to expand malware functionality easily.
🚀 Attack Chain and Infection Process
Like many advanced malware families, NullRAT 2026 typically follows a multi-stage attack process.
📦 Stage 1 – Malware Delivery
The attack begins by delivering the malware to the victim.
📥 Common Distribution Methods
📧 Phishing email attachments
💾 Malicious software downloads
🧪 Trojanized tools and scripts
🌐 Fake developer utilities
Users often unknowingly execute these files.
⚡ Stage 2 – Execution and Installation
Once executed, the malware installs itself on the system.
⚙ Execution Process
🔧 Payload deployment
🔧 Security bypass techniques
🔧 System configuration changes
🔧 Connection to attacker server
This establishes communication between the victim device and attacker infrastructure.
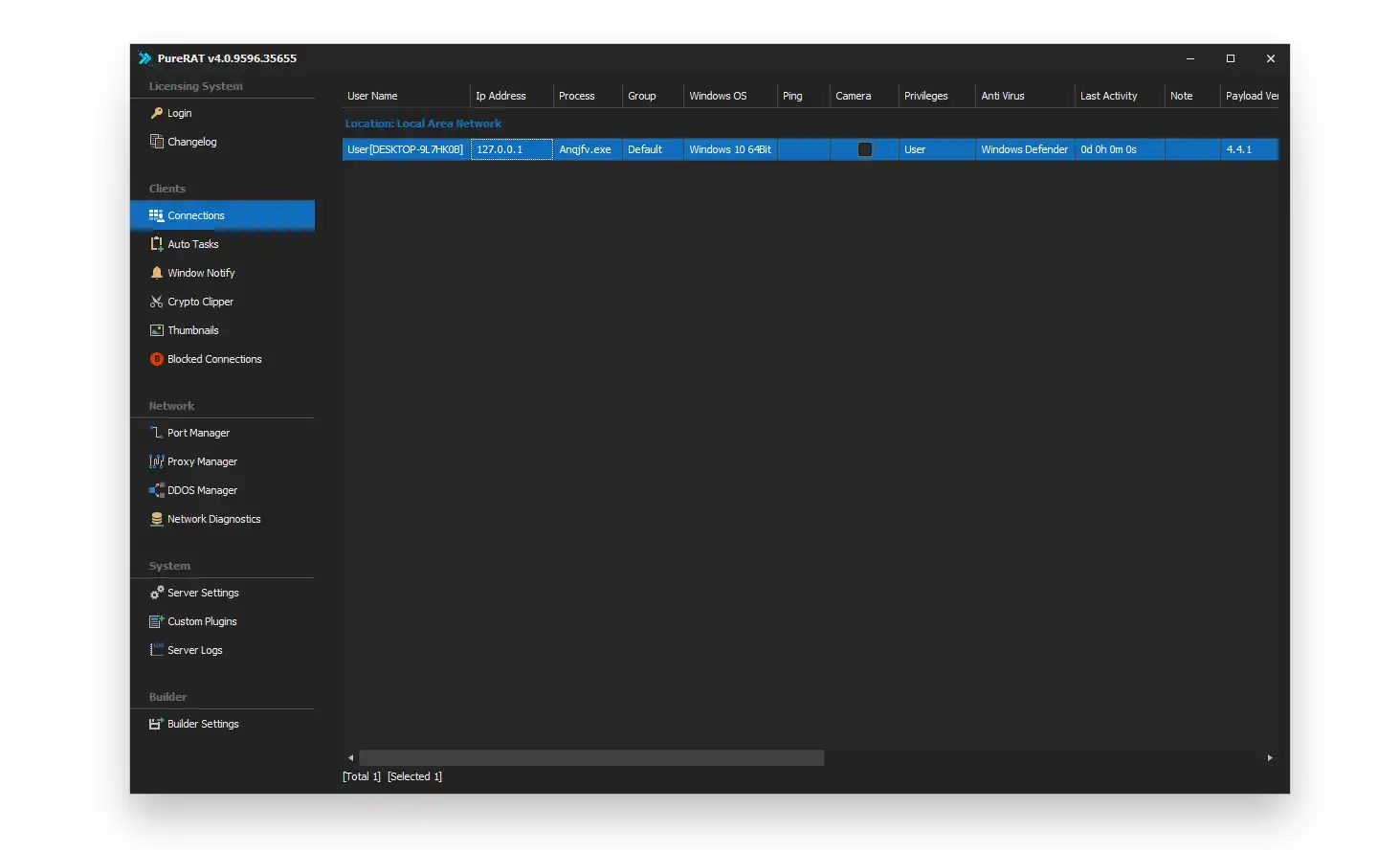
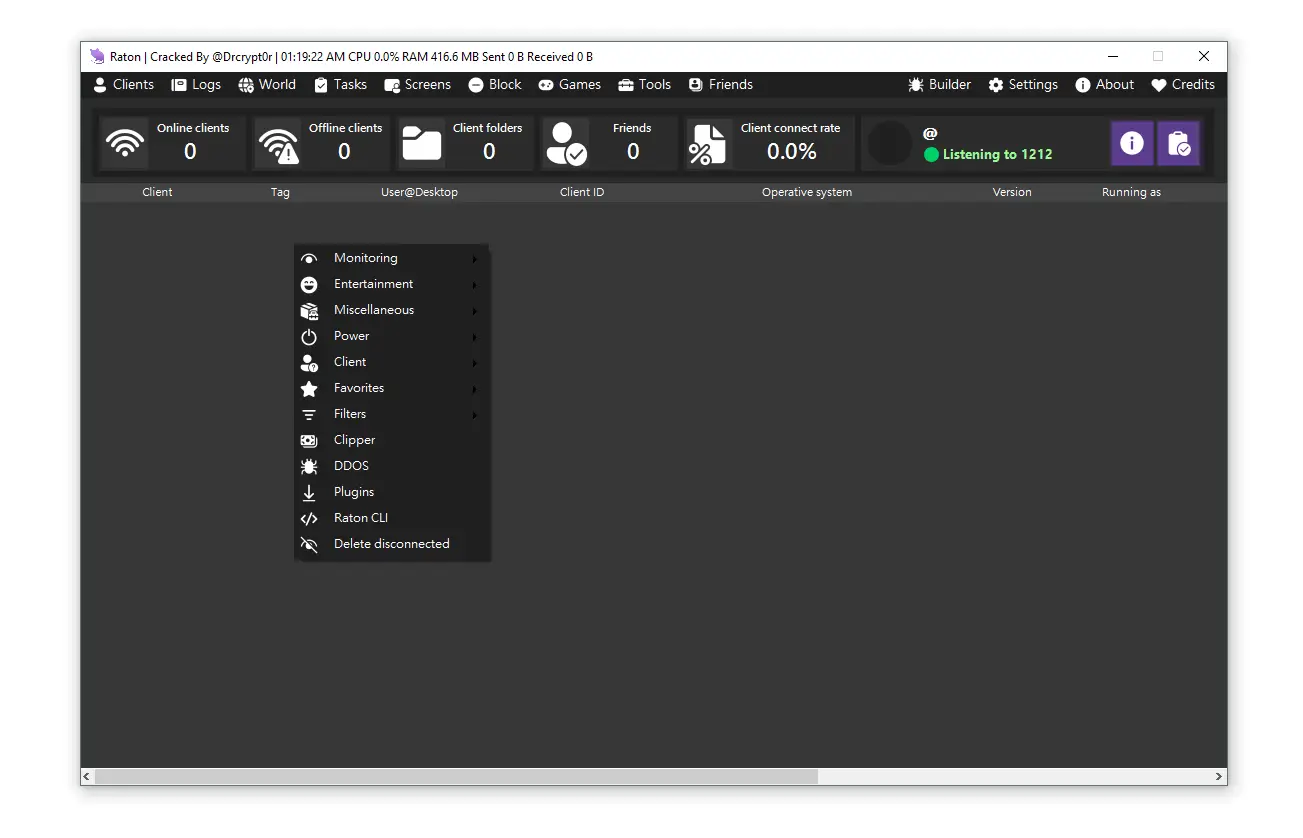
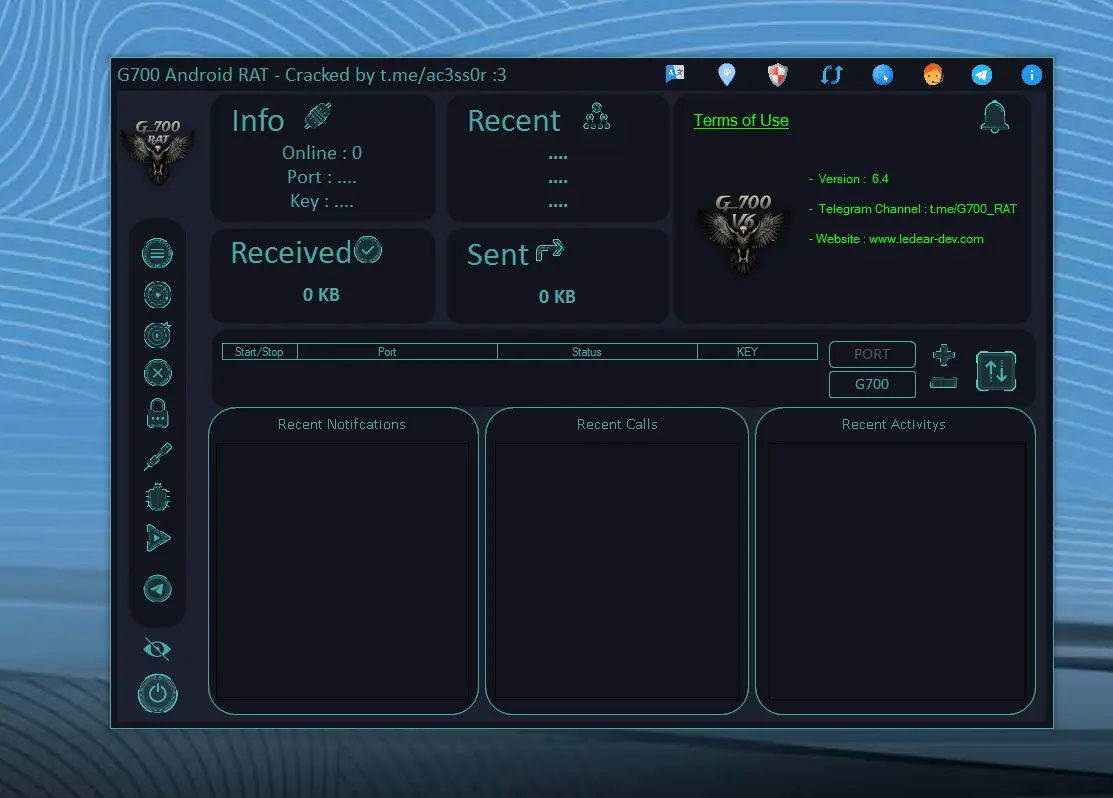
🎮 Stage 3 – Remote Control
After the connection is established, attackers gain remote control.
🕹 Possible Attacker Actions
🖥 Execute remote commands
📂 Access files and documents
🔑 Steal credentials and passwords
📡 Monitor user activity
The infected machine effectively becomes a remotely controlled system.
🔄 Persistence Mechanisms
To maintain access after system reboot, malware may implement persistence techniques.
🧩 Common Persistence Methods
🗂 Registry startup entries
📁 Scheduled tasks
⚙️ Startup folder scripts
🖥 Background services
These techniques ensure the malware remains active on the system.
🌐 Command and Control Infrastructure
A Command and Control (C2) server acts as the control hub for attackers.
📡 C2 Communication Functions
📡 Receive commands from attackers
📡 Send stolen information back to the server
📡 Deploy additional malware components
📡 Maintain persistent connection
Encrypted communication channels are often used to avoid detection.
📤 Data Exfiltration Techniques
Once information is collected, the malware sends it to the attacker.
📂 Stolen Data May Include
🔑 Credentials and passwords
📁 Sensitive files and documents
💳 Financial information
📊 System configuration data
Data exfiltration is usually performed through hidden network communication.
🚨 Indicators of Compromise (IoCs)
Security teams monitor specific indicators to detect potential malware infections.
🔍 Possible Signs of NullRAT 2026 Infection
⚠️ Unknown background processes
⚠️ Suspicious network traffic
⚠️ Unusual CPU or memory usage
⚠️ Security software being disabled
⚠️ Unknown Python scripts running
These signs may indicate RAT malware activity.
🛡 Example YARA Detection Rule for NullRAT 2026
YARA rules help identify malware samples based on patterns.
rule NullRAT_2026_Detection
{
meta:
description = "Detects NullRAT 2026 malware activity"
author = "Security Research"
family = "NullRAT"
strings:
$a1 = "NullRAT"
$a2 = "command_execution"
$a3 = "client_connect"
$a4 = "remote_control"
condition:
2 of ($a*)
}
These rules help security analysts detect suspicious malware behavior.
🔎 Detection and Security Analysis
Detecting RAT malware requires multiple cybersecurity tools.
🛠 Security Detection Methods
🛡 Endpoint Detection and Response systems
🛡 Antivirus and anti-malware solutions
🛡 Network monitoring tools
🛡 Malware analysis sandboxes
Behavior-based detection is particularly effective against advanced threats.
🔐 Prevention and Protection Strategies
Prevention is the most effective defense against malware infections.
🧰 Cybersecurity Best Practices
✔️ Avoid downloading unknown software
✔️ Verify the authenticity of tools and scripts
✔️ Keep operating systems updated
✔️ Use strong endpoint security solutions
✔️ Enable firewall protection
✔️ Monitor network traffic regularly
Practicing safe computing habits significantly reduces infection risks.
🔮 Future Cyber Threat Landscape
Cyber threats continue to evolve as attackers adopt new technologies.
Future malware may include:
⚡ AI-assisted attack automation
⚡ Advanced encryption techniques
⚡ Cross-platform malware variants
⚡ More stealthy persistence mechanisms
Security teams must continuously improve detection capabilities.
Download NullRAT 2026
🧾 Conclusion
NullRAT 2026 demonstrates how modern Remote Access Trojan frameworks can provide attackers with extensive control over compromised systems. With capabilities such as remote command execution, surveillance, and credential theft, this malware highlights the growing risks associated with unauthorized remote access tools.
Understanding how NullRAT 2026 operates helps cybersecurity professionals detect and mitigate threats more effectively. By following strong security practices and maintaining awareness of emerging threats, individuals and organizations can significantly reduce their exposure to cyber attacks.
❓ FAQs
What is NullRAT 2026?
NullRAT 2026 is a Python-based Remote Access Trojan designed to allow attackers to remotely control infected systems and steal sensitive information.
Is NullRAT 2026 dangerous?
Yes. Like other RAT malware, it can provide attackers with full system control and access to personal or corporate data.
How does NullRAT 2026 infect systems?
It can spread through phishing emails, malicious downloads, trojanized tools, and suspicious scripts.
What are the main signs of infection?
Indicators include suspicious network connections, unknown background processes, unusual CPU activity, and disabled security software.
How can users protect themselves from RAT malware?
Users should avoid executing unknown files, keep security software updated, verify downloads, and monitor system activity regularly.