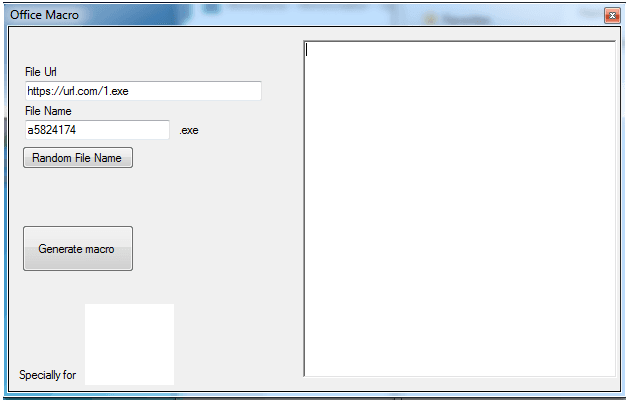
Exploit Office Macro 2025
Exploit Office Macro 2025
Advanced Web Hacking Tools 2025
Advanced Web Hacking Tools 2025 Advanced Web Hacking Tools 2025 A internet utility is a application or software program that runs on a…
WordPress All in One Bruteforce 2025
WordPress All in One Bruteforce 2025
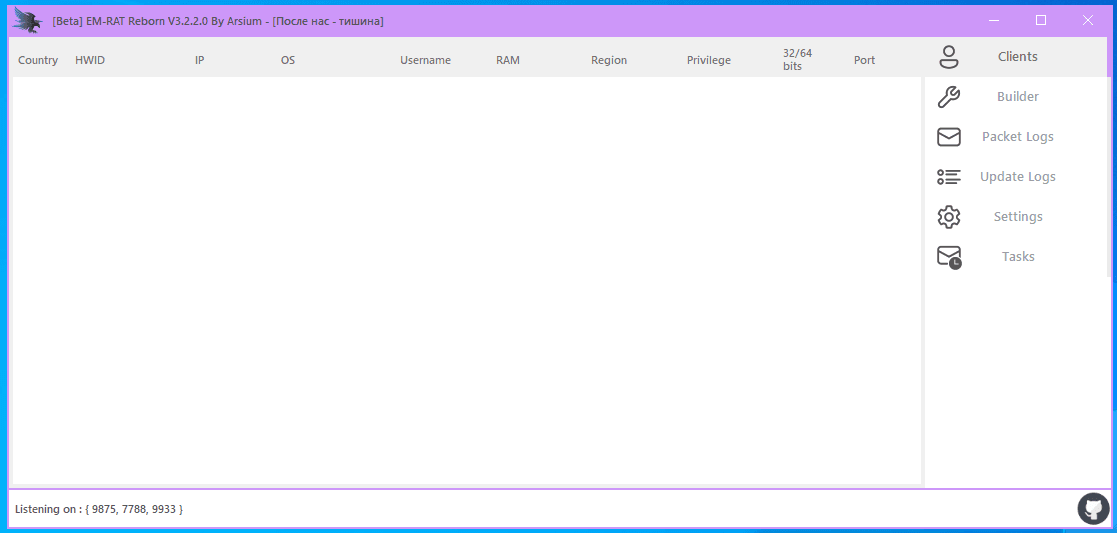
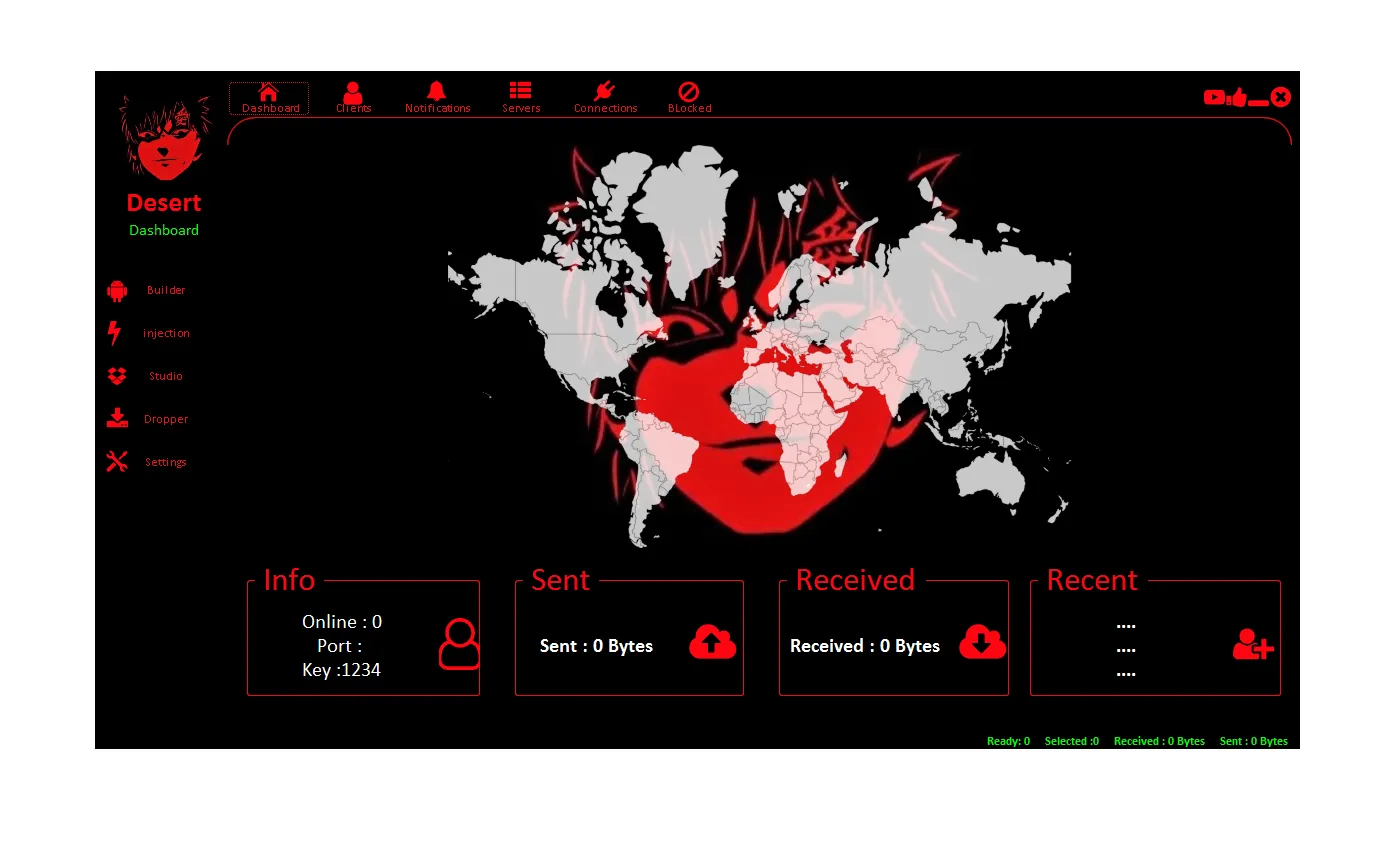
Eagle Monitor RAT Reborn V3.2.2.0
Eagle Monitor RAT Reborn V3.2.2.0 the creator and all those associated with the development and production of this program are not responsible for…
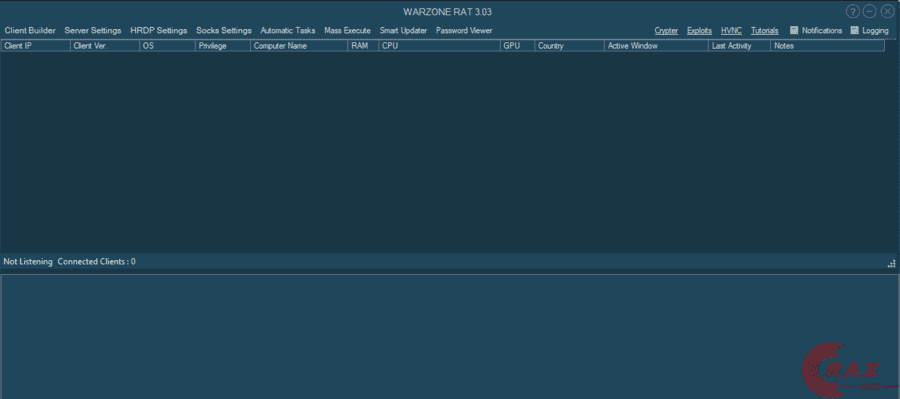
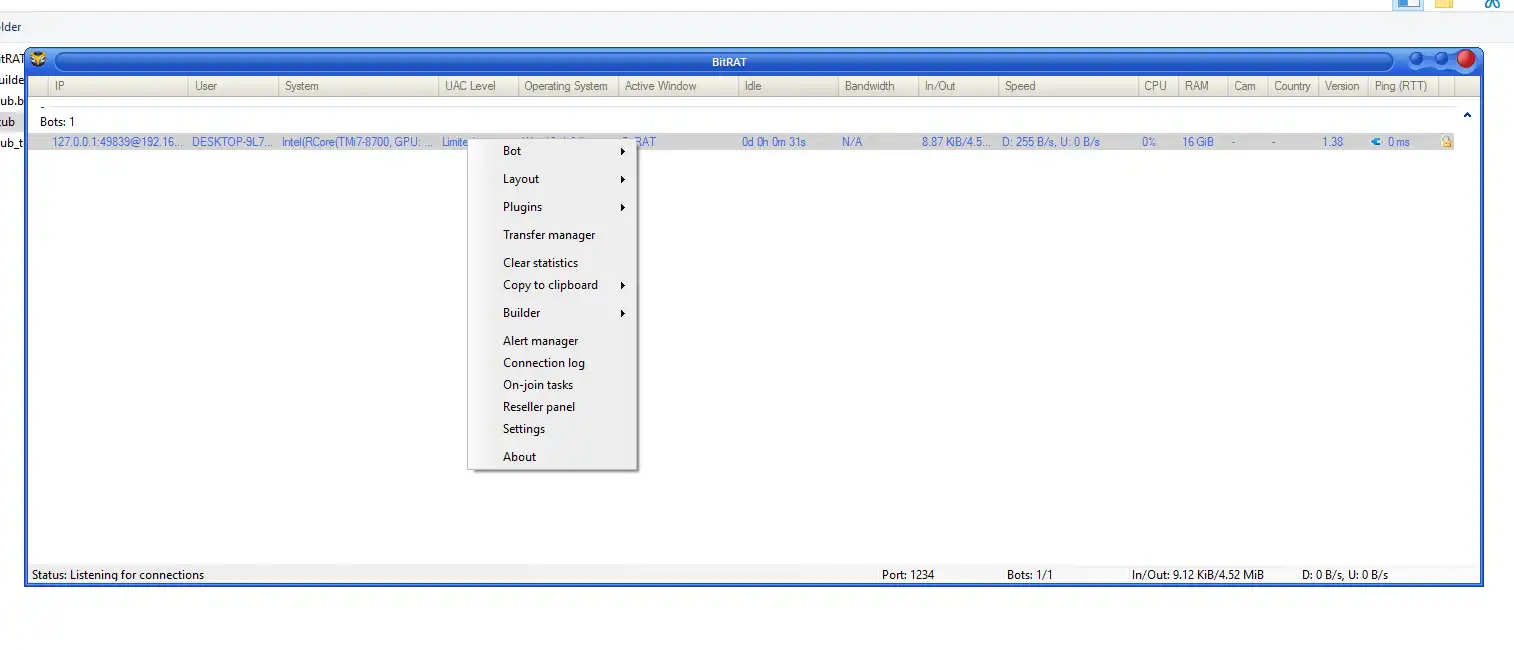
WarZone RAT 3.03 Cracked
WarZone RAT 3.03 Cracked WarZone RAT 3.03 Cracked is Native, independent stub Stub of WarZone RAT 3.03 Cracked has been written in C++ which…
SQLi Dumper V.10.5 Cracked
SQLi Dumper V.10.5 Cracked
Hellfire Yahoo Checker 2025
Hellfire Yahoo Checker 2025
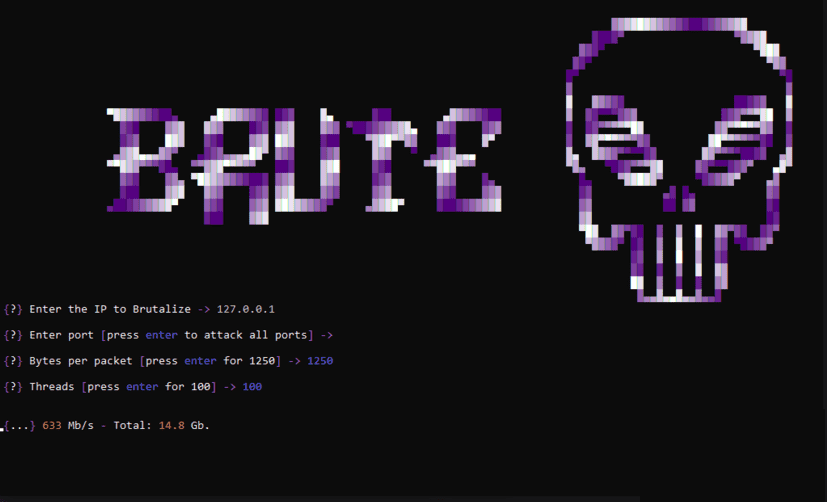
Layer 4 DDOS Tool Python 2024
Layer 4 DDOS Tool Python 2024