Remote Access Trojans (RATs) remain one of the most dangerous cyber threats today. Nigger RAT v1.8 is a modern evolution of RAT malware designed for stealth, control, and data theft. Unlike older malware, this variant provides attackers with a modular, user-friendly interface that allows even low-skill operators to conduct sophisticated attacks.
This guide breaks down every aspect of Nigger RAT v1.8 in detail, explaining how it operates, spreads, steals data, and how to defend against it. Each feature is described with practical examples and technical insight.
🧠 What is Nigger RAT v1.8?
Nigger RAT v1.8 is a Remote Access Trojan (RAT) that gives attackers unauthorized access to victim machines. Its main purpose is full system control, data theft, and surveillance, while maintaining stealth.
⚡ Key Capabilities (Expanded):
🖥️ Remote System Control
- Nigger RAT v1.8 allows attackers to manipulate the victim’s computer remotely as if they were physically in front of it.
- The attacker can launch applications, browse files, or execute commands, making it extremely versatile.
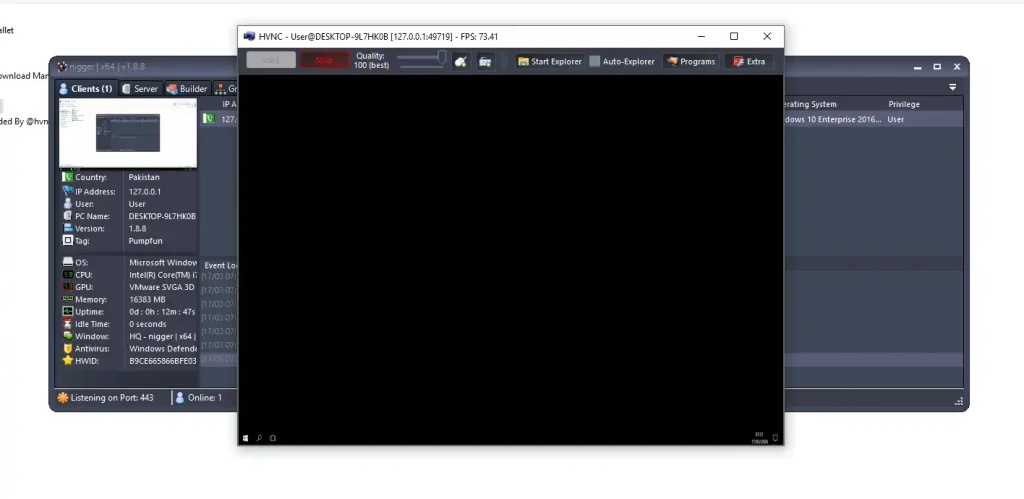
- Remote control is possible even when the user is active on the system, using Hidden Virtual Network Computing (HVNC) technology. HVNC creates an invisible desktop session that mirrors the real desktop, allowing the attacker to perform tasks without the victim noticing.
🔑 Password and Credential Theft
- This RAT can automatically extract stored passwords from web browsers like Chrome, Firefox, and Edge.
- It can also target email clients, FTP programs, and other credential storage applications.
- Advanced encryption is used to exfiltrate data without triggering antivirus alerts, making the stolen credentials highly valuable to attackers.
⌨️ Keystroke Logging
- Every keystroke on the victim machine can be captured.
- This includes login credentials, private messages, and sensitive searches.
- The logs are saved in hidden directories and periodically sent to the attacker’s server, ensuring continuous monitoring of the victim’s activity.
📂 File Monitoring and Extraction
- Attackers can browse the victim’s file system remotely.
- Files can be copied or deleted, and certain file types can be targeted automatically (e.g., documents, images, and spreadsheets).
- Combined with stealth features, this ensures complete data exfiltration without alerting the victim.
⚙️ How Nigger RAT v1.8 Works
Nigger RAT v1.8 operates through a client-server architecture.
🔄 Working Process (Expanded):
- 📥 Infection: The victim is tricked into running the malware via phishing emails, malicious downloads, or fake software.
- 🔗 Connection: The malware connects to the attacker’s command-and-control (C2) server.
- 📡 Continuous Monitoring: The RAT maintains a persistent connection, allowing the attacker to track the system, perform tasks, or deploy additional modules.
- 🎯 Full Access: From the control panel, attackers can perform remote control, data theft, surveillance, and more, all silently.
⚡ This system allows continuous, undetectable control, making it extremely dangerous for individuals and organizations.
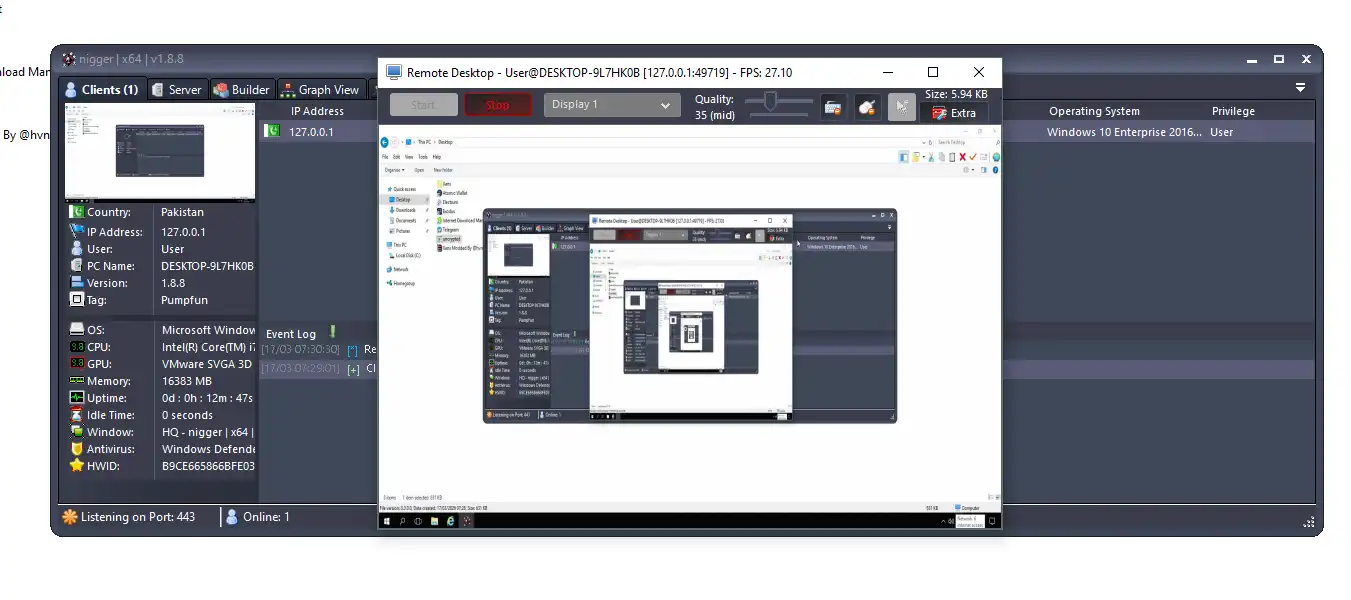
🖥️ Server Dashboard Overview
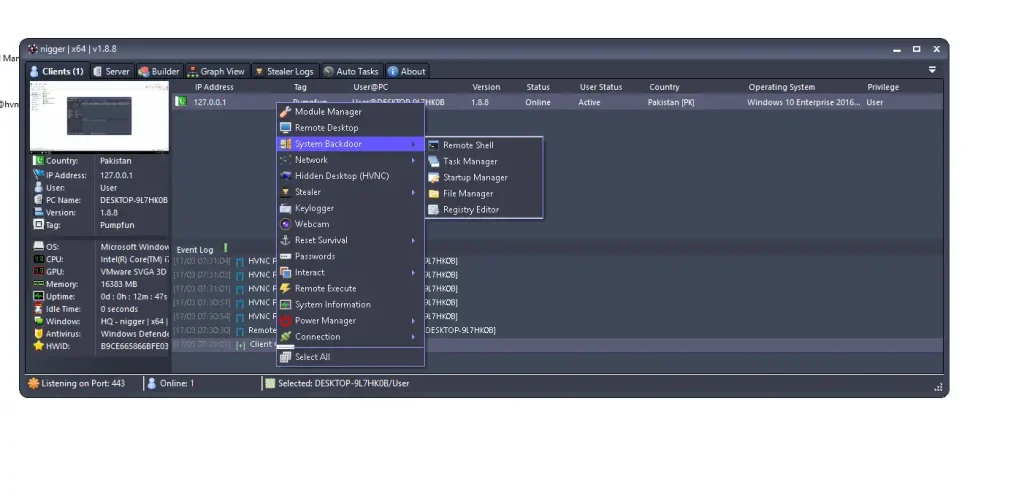
The server dashboard is the attacker’s control center, providing a real-time overview of all connected victims.
📊 Dashboard Features (Expanded):
- 📋 Connected Devices List: Shows IP address, username, operating system, and current status.
- 🌐 IP Tracking: Allows attackers to approximate the location of victims.
- 👤 User & System Info: Displays device name, OS version, installed programs, memory, and CPU details.
- 📶 Online Status Monitoring: Lets attackers know which machines are active or idle.
- 🗂️ Event Logs: Shows connection attempts, errors, and other important system events.
💡 This centralized hub is designed to maximize operational efficiency and minimize the risk of losing access to infected machines.
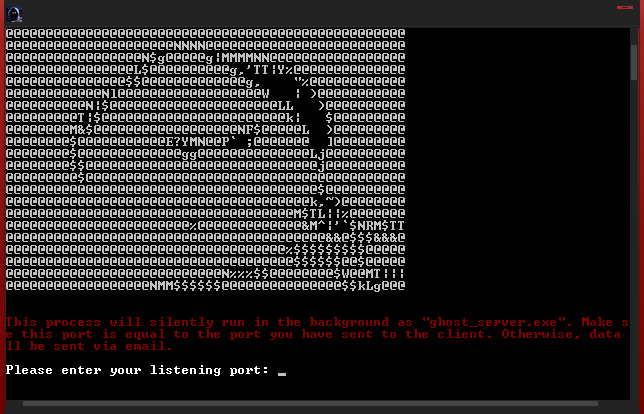
🔧 Server Configuration Features
Attackers can customize the server to maximize stealth and functionality.
⚙️ Key Settings (Expanded):
🔐 Port Selection
- Nigger RAT v1.8 typically uses port 443, the standard HTTPS port.
- This allows malware traffic to blend with normal web traffic, avoiding firewall and IDS detection.
🌍 Dynamic DNS Integration
- Supports dynamic DNS services to maintain connectivity even if the attacker’s IP changes.
- This ensures persistent control over victims in real-world environments.
🔔 Connection Notifications
- Alerts the attacker whenever a new machine connects to the server.
- This real-time feedback helps rapidly deploy further actions.
🔄 Automatic Port Forwarding
- The RAT can automatically configure routers using UPnP to forward the required ports.
- This removes the need for technical knowledge, allowing even novice attackers to operate efficiently.
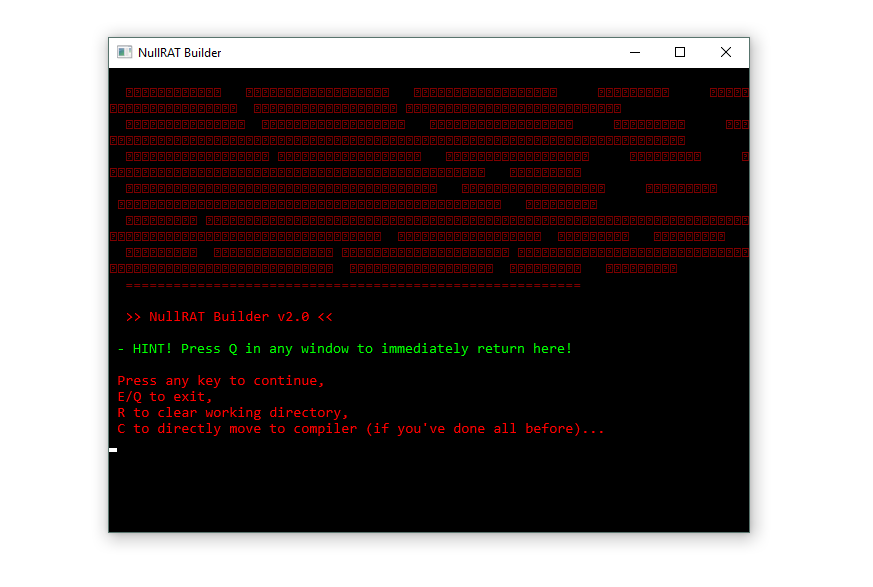
🧬 Client Builder (Payload Creation)
The client builder is where attackers generate the executable that infects victims.
🏗️ Installation Options (Expanded):
📁 Hidden File Placement
- Allows installation in AppData, Program Files, or system directories.
- Hiding files ensures minimal suspicion from users.
🗂️ Custom File Naming
- Executables can be named to mimic legitimate files, like
svchost.exeor random letters. - This increases the likelihood that victims will open the file without suspicion.
🔁 Auto-Start on Boot
- Ensures malware runs automatically when the system restarts.
- This uses registry Run keys or Startup folders, maintaining persistent access.
🎭 Stealth Techniques (Expanded):
🧾 Fake Metadata
- Attackers can modify assembly information, including product name, company, and version.
- Fake details make the malware appear legitimate to both users and antivirus software.
🖼️ Custom Icons
- Executables can use icons resembling PDFs, folders, or other common file types.
- Social engineering ensures the victim is more likely to click the file.
👁️ Hidden Attributes
- Files and directories can be marked as hidden, preventing casual discovery in Windows Explorer.
- This enhances persistence and stealth.
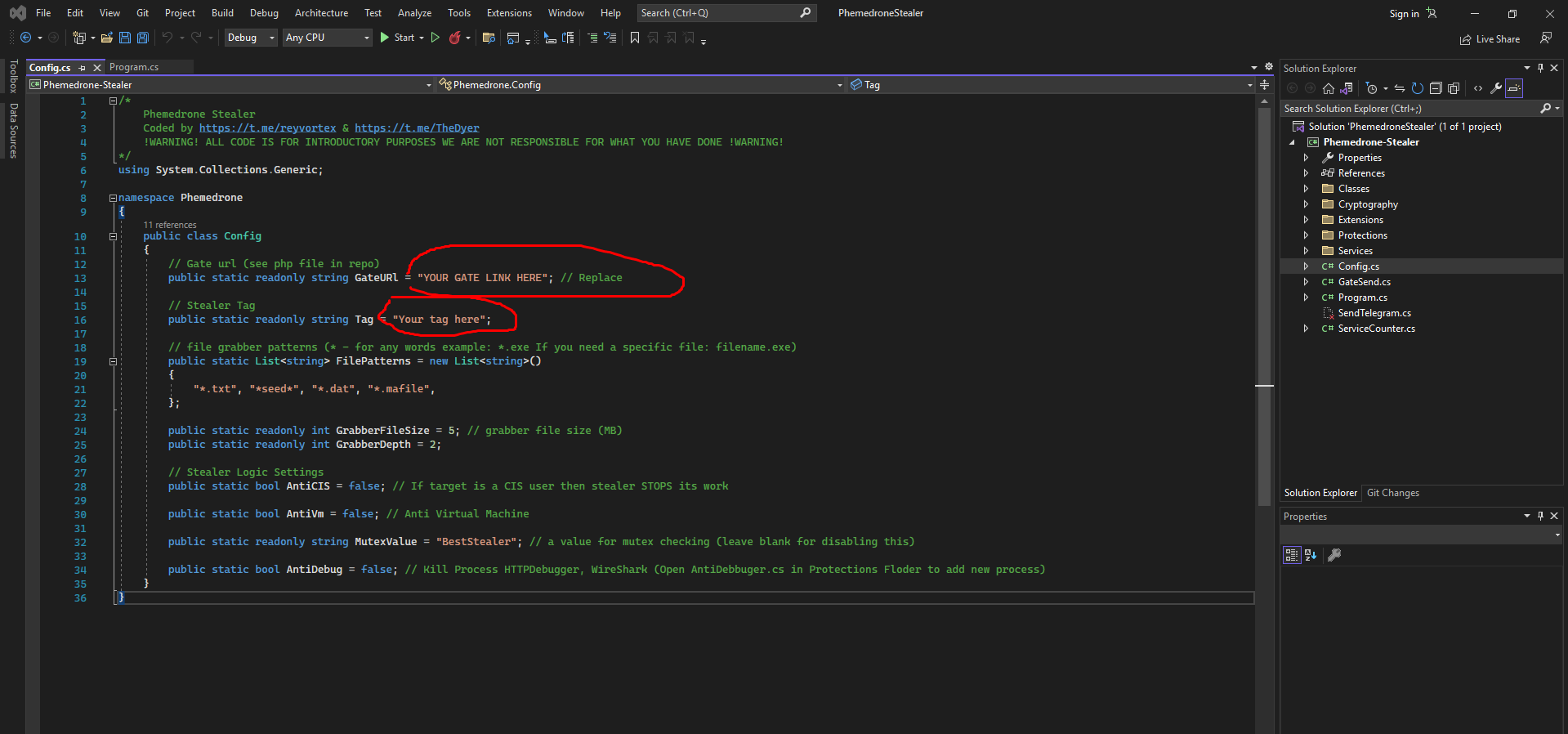
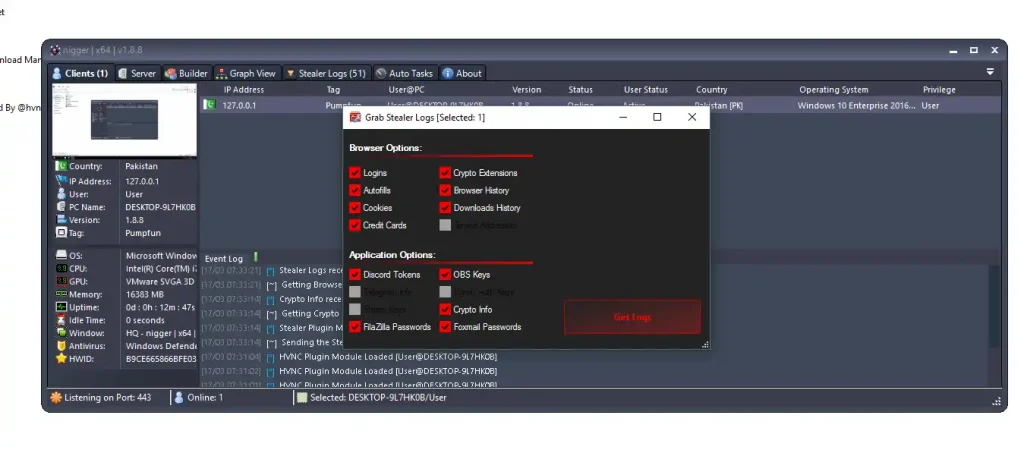
🔍 Data Theft Capabilities
Nigger RAT v1.8 focuses heavily on stealing sensitive information.
🚨 Targeted Data (Expanded):
🔑 Saved Passwords
- Extracts passwords from web browsers and applications.
- Can recover email, social media, and financial credentials.
💳 Credit Card Information
- Targets browser-stored card data and payment details.
- This data can be used for financial theft or identity fraud.
🌐 Browser Cookies
- Stolen cookies allow attackers to hijack active sessions, bypassing the need for passwords.
- This enables access to social media accounts, emails, or banking portals.
📜 Browsing History
- Provides intelligence on the victim’s habits and interests.
- Useful for profiling or planning further attacks.
💰 Cryptocurrency Wallets
- Targets desktop wallets like Electrum or Bitcoin Core.
- Enables attackers to transfer crypto funds silently.
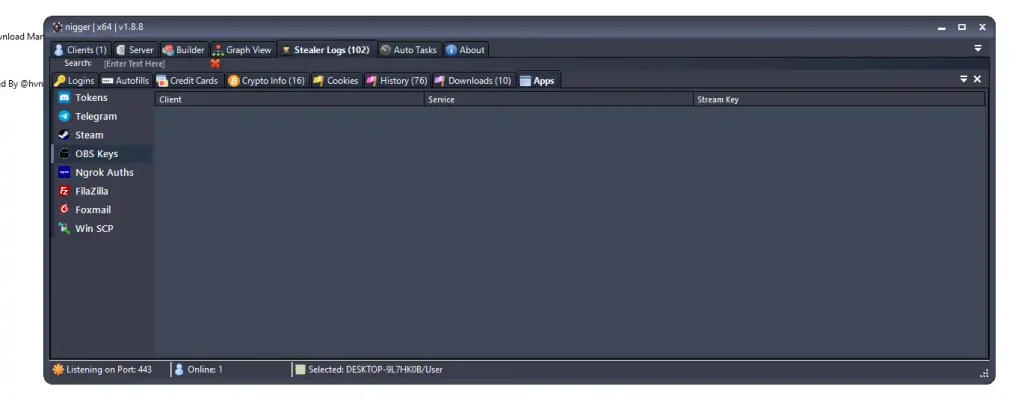
⚡ Advanced Targets (Expanded):
💬 Messaging App Tokens
- Steals tokens from platforms like Discord, Telegram, and Slack.
- Allows attackers to take over accounts and impersonate victims.
📂 FTP Credentials
- Gains access to FTP clients such as FileZilla or WinSCP.
- Can be used to exfiltrate website data or databases.
🎥 Streaming Keys
- Steals OBS, Twitch, or other streaming credentials.
- Attackers can hijack live streams or monetize stolen accounts.
🎯 Remote Access Features
Once deployed, Nigger RAT v1.8 allows full system control.
🖥️ Control Functions (Expanded):
🖱️ Remote Desktop
- Full desktop view of the victim’s system.
- Execute applications, browse files, or change system settings.
🕶️ Hidden Desktop (HVNC)
- Creates an invisible session to interact without detection.
- Useful for financial fraud or confidential operations.
📷 Webcam Monitoring
- Capture images or stream video from the victim’s camera.
- This can be used for espionage or blackmail.
⌨️ Keylogging
- Records every keystroke including passwords, messages, and searches.
- Data is encrypted and sent to the attacker for maximum stealth.
⚡ System Actions (Expanded):
- 🔄 Restart system for payload updates
- 🔌 Shutdown device to disrupt victim
- 🚪 Log out user to force malware persistence
🧠 Advanced Threat Capabilities
Nigger RAT v1.8 is designed for modern attackers.
🚨 Features (Expanded):
- 🧬 Fileless Storage: Some data is stored in memory or registry to evade antivirus detection.
- 🧩 Plugin Architecture: Allows additional modules like ransomware or advanced stealers to be deployed.
- 🔐 Potential Ransomware Support: Can encrypt files if additional modules are added.
📥 Infection Methods
🚨 Common Spread Techniques:
📧 Phishing Emails
- Attachments disguised as invoices, shipping labels, or documents.
- Social engineering tricks victims into running the RAT.
💾 Infected USB Drives
- Malware copies itself onto removable drives.
- Creates shortcut files that look like normal directories.
🌐 Malicious Downloads
- Compromised websites automatically install the RAT via browser exploits.
🔓 Fake Cracks or Software
- Hidden in key generators or cracked software.
- Users downloading pirated software often get infected without realizing.
🛡️ Protection & Security Tips
✅ Prevention
- 🚫 Avoid unknown files and downloads
- 📧 Do not click suspicious email links
- 🔐 Use reputable antivirus
- 🔄 Keep system and software updated
🔍 Detection
- 📊 Monitor unusual CPU/network usage
- 🌐 Check for unknown connections
- ⚠️ Investigate unknown running processes
🔧 Recovery
- 🔌 Disconnect infected device immediately
- 🔑 Change all passwords
- 💾 Restore from backup
- 🛠️ Scan and clean with advanced security tools
Download Nigger RAT v1.8
🧾 Conclusion
Nigger RAT v1.8 is a highly dangerous malware combining remote control, data theft, and stealth.
Its ease of use makes it accessible to a wide range of attackers, posing risks to both individuals and organizations.
⚡ Defense requires:
- Awareness
- Safe browsing habits
- Strong security practices
❓ FAQs
❓ What is Nigger RAT v1.8?
A remote access trojan designed to steal data, control systems, and spy on users.
❓ Is Nigger RAT v1.8 dangerous?
Yes, it can steal passwords, credit card information, and control systems remotely.
❓ How does it spread?
Via phishing emails, malicious downloads, fake software, or infected USB drives.
❓ Can it be removed?
Yes, using advanced antivirus software and proper system cleanup.
❓ How can I stay protected?
Avoid suspicious files, update your system, and use trusted antivirus solutions.