Malicious
CatLogs Stealer 2025
CatLogs Stealer 2025 The ever-changing cybersecurity landscape continues to provide challenges for individuals, businesses, and organizations around the world. Malicious actors’ strategies for compromising...
KRIPTO CLIPPER 2025
KRIPTO CLIPPER 2025 KRIPTO CLIPPER 2025 A crypto clipper is a type of malware or malicious software designed to steal cryptocurrency from victims by...
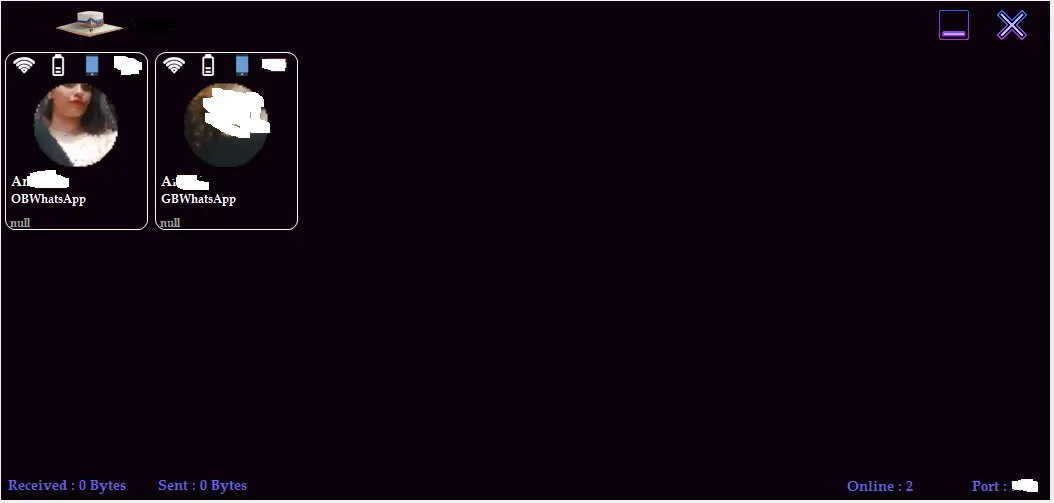
ROGUE V6.2 ANDROID BOTNET PREMIUM
ROGUE V6.2 ANDROID BOTNET PREMIUM ROGUE V6.2 ANDROID BOTNET PREMIUM made to execute commands with incredible features without a need of computer. No...
Sseur Keylogger 2025 Cracked
Sseur Keylogger 2025 Cracked
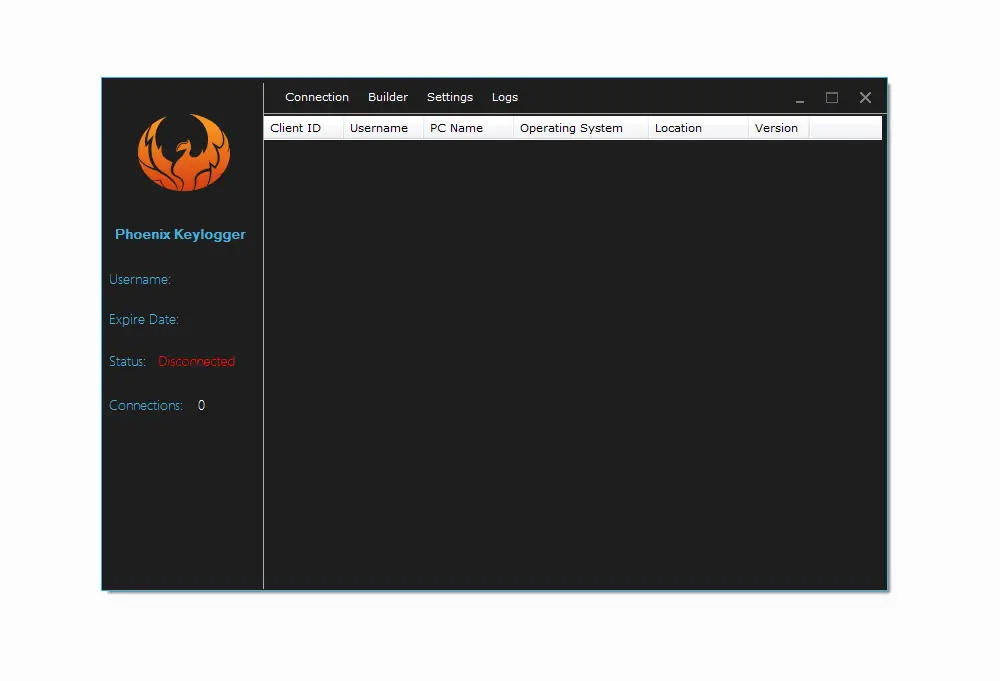
Poenix Keylogger 2025 Cracked
Poenix Keylogger 2025 Cracked
Screen Lock Builder 1.1.2.0
Screen Lock Builder 1.1.2.0
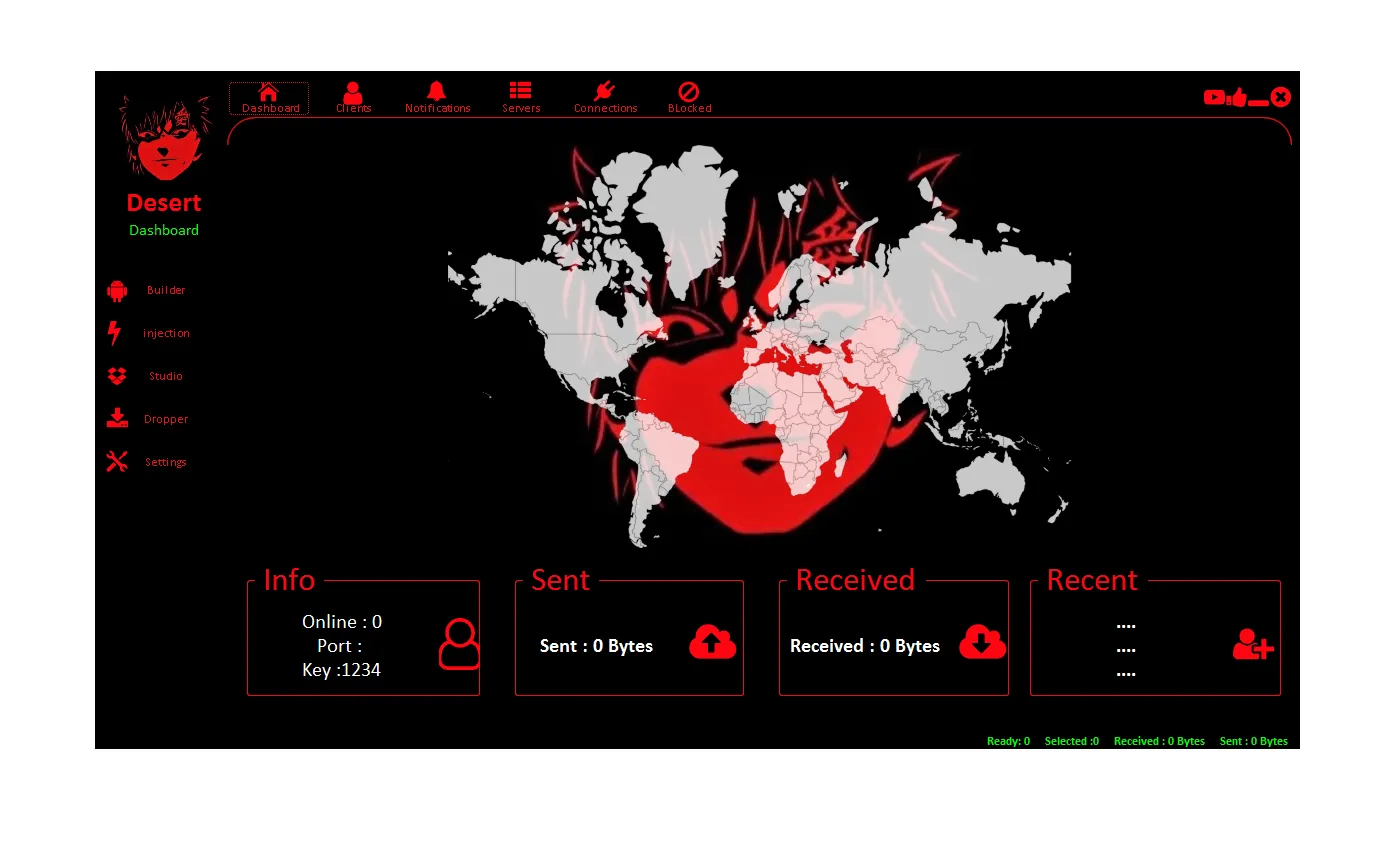
Cypher Rat 2025 cracked
Cypher Rat 2025 cracked The digital landscape is ever-evolving, and with it, the tools and techniques used by cybersecurity professionals and hackers alike. One...