📱 Introduction RedBat RAT 2026
The modern mobile ecosystem is facing an unprecedented rise in Android malware, particularly Remote Access Trojans (RATs) like RedBat RAT 2026. This advanced threat is a modified evolution of Crax RAT, designed to exploit Android devices through stealth, persistence, and deep system access.
From a cybersecurity perspective, RedBat RAT 2026 Android malware represents a significant risk to mobile privacy, digital identity, financial security, and enterprise mobility environments. Users in the United States and Europe are especially vulnerable due to widespread use of mobile banking apps, cloud storage platforms, and digital authentication systems.
Understanding how this malware operates is essential for threat detection, mobile endpoint protection, and proactive defense strategies. This article provides a complete breakdown using semantic depth, covering infection vectors, data exfiltration, privilege escalation, command-and-control (C2), and mitigation techniques.
🧩 apk dropper – The Initial Infection Vector

- 📥 Disguised APK Distribution (Social Engineering Attack Vector):
RedBat RAT 2026 Android malware primarily spreads through malicious APK sideloading, a common technique in Android threat landscapes. These APKs are disguised as legitimate applications such as system updates, cracked apps, or productivity tools, targeting users who install software outside trusted ecosystems like Google Play. From a threat intelligence standpoint, this method relies heavily on user trust exploitation and phishing-style deception. The apps are visually identical to genuine ones, making detection difficult for non-technical users. This infection vector highlights the importance of secure app distribution channels and user awareness training. - 🧬 Dynamic Payload Activation (Evasion Technique):
Instead of embedding the entire malicious payload in the initial APK, RedBat uses modular malware architecture with dynamic payload loading. This technique allows it to bypass signature-based antivirus detection systems and evade static analysis tools. The malware can download additional components from remote servers, enabling real-time updates and feature expansion. This behavior aligns with modern advanced persistent threat (APT) tactics, where adaptability and stealth are prioritized. It significantly increases the malware’s lifespan and effectiveness in real-world environments. - 🔐 Gradual Permission Escalation (Privilege Abuse Strategy):
RedBat implements a multi-stage permission escalation model, starting with basic permissions and gradually requesting more sensitive access such as Accessibility Services, Device Admin rights, and Overlay permissions. This approach reduces suspicion while enabling full device compromise over time. From a mobile security perspective, this tactic exploits Android’s permission-based architecture, turning legitimate system features into attack vectors. Monitoring abnormal permission combinations is critical for detecting such threats.
🛠️ apk studio – APK Manipulation & Repackaging Studio
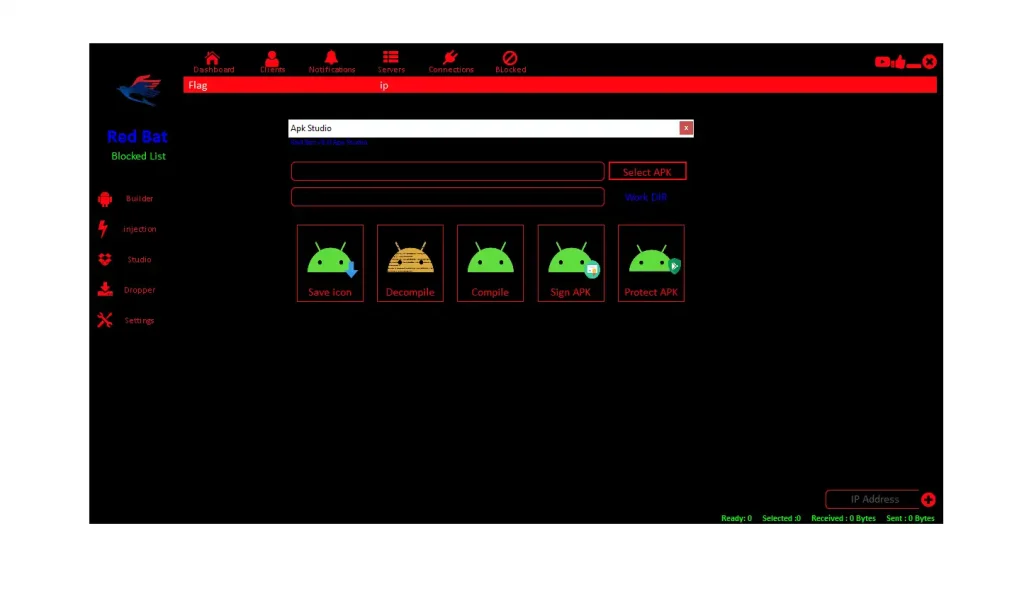
- 🧪 Decompiling Legitimate Applications (Reverse Engineering Abuse):
Attackers use APK manipulation tools to reverse engineer Android applications, allowing them to access source code and internal logic. This enables precise insertion of malicious payloads without disrupting app functionality. In cybersecurity terms, this is a form of code injection attack, where trusted software becomes a carrier for malware. This technique is widely used in trojanized applications, making it a major concern for app integrity and software supply chain security. - 🔏 Repackaging and Signing (Bypassing Android Security):
After modification, apps are recompiled and signed using custom certificates, bypassing Android’s application signature verification process. This enables installation without triggering security warnings. From a mobile OS security standpoint, this highlights weaknesses in sideloading environments where signature trust chains are not enforced. It also demonstrates how attackers exploit user-side installation permissions to bypass built-in safeguards. - 🕵️ Obfuscation and Anti-Debugging (Anti-Forensics Techniques):
RedBat uses advanced code obfuscation, encryption, and anti-debugging mechanisms to prevent analysis. These techniques fall under malware anti-forensics, making it difficult for cybersecurity researchers to reverse engineer the threat. It can detect sandbox environments and disable malicious functions to avoid detection. This significantly delays incident response and threat intelligence gathering.
📊 builder monitor – Credential & Account Harvesting
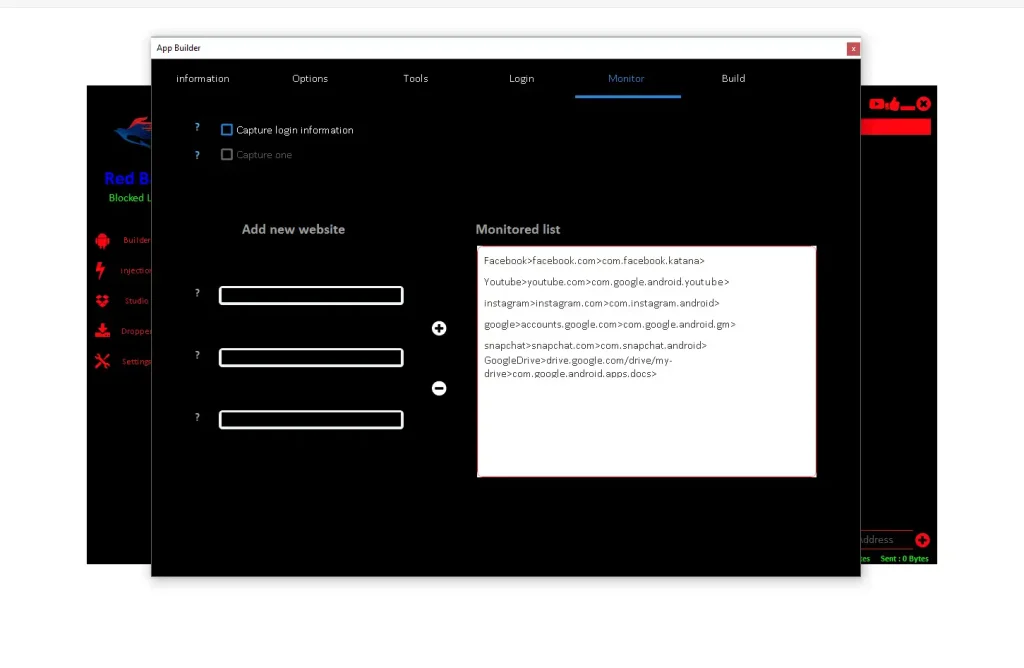
- 🔑 Credential Harvesting (Identity Theft Vector):
RedBat RAT 2026 targets sensitive user data such as login credentials, authentication tokens, and account details from platforms like banking apps, email services, and cloud storage. This aligns with credential stuffing and identity theft attacks, where stolen data is reused across multiple services. The malware can bypass login systems by capturing session tokens, making it more dangerous than traditional password theft. - 📡 Real-Time Data Exfiltration (C2 Communication):
Stolen data is transmitted instantly to attacker-controlled servers via encrypted communication channels. This process, known as data exfiltration, ensures attackers retain access to valuable information even if the malware is removed. Continuous data streaming also enables live monitoring of victim activity, increasing the threat level significantly. - 📉 Behavioral Surveillance (User Profiling):
Beyond credentials, RedBat collects behavioral data such as browsing patterns, app usage, and interaction habits. This is used for user profiling and targeted cyberattacks, including spear phishing and social engineering campaigns. Behavioral analytics increases the value of stolen data in underground cybercrime markets.
🎭 builder options – Custom App & Notification Spoofing
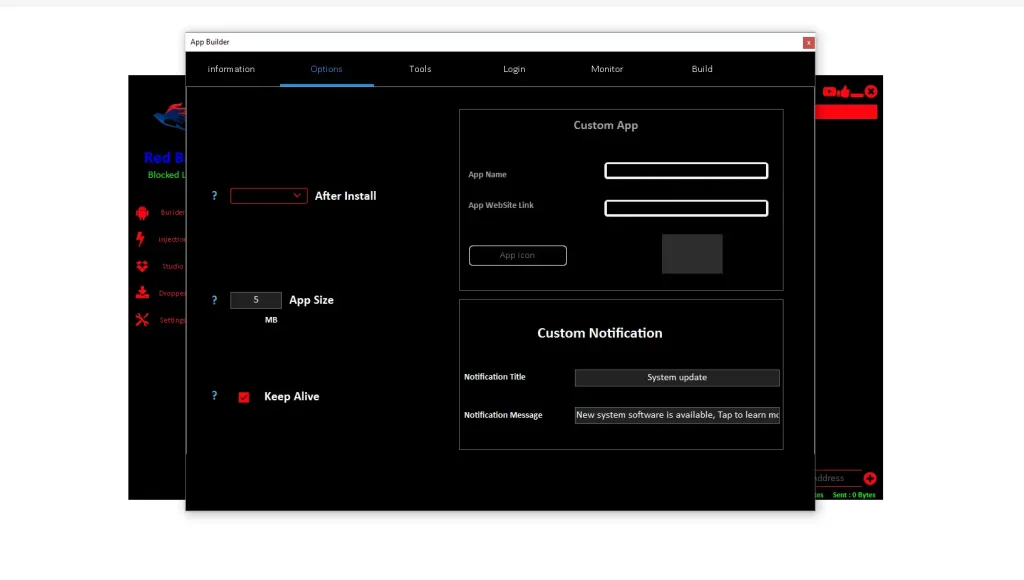
- 🎨 App Identity Spoofing (Brand Impersonation):
Attackers can fully customize app appearance to mimic trusted brands, a technique known as brand spoofing. This is commonly used in phishing campaigns to gain user trust. By replicating official app designs, attackers significantly increase the success rate of malware installation. - 🔔 Fake System Notifications (Psychological Manipulation):
RedBat RAT 2026 generates fake alerts such as “System Update Required,” leveraging urgency-based social engineering tactics. These notifications exploit human psychology, prompting users to act quickly without verifying authenticity. This method is widely used in mobile phishing attacks. - 🌐 Phishing Redirection (Credential Interception):
Users are redirected to fake login pages designed to capture credentials. These pages use UI spoofing techniques to appear legitimate. This form of attack is part of credential phishing and web injection attacks, commonly seen in advanced mobile malware.
🧰 builder tools – Advanced Persistence & Evasion Techniques
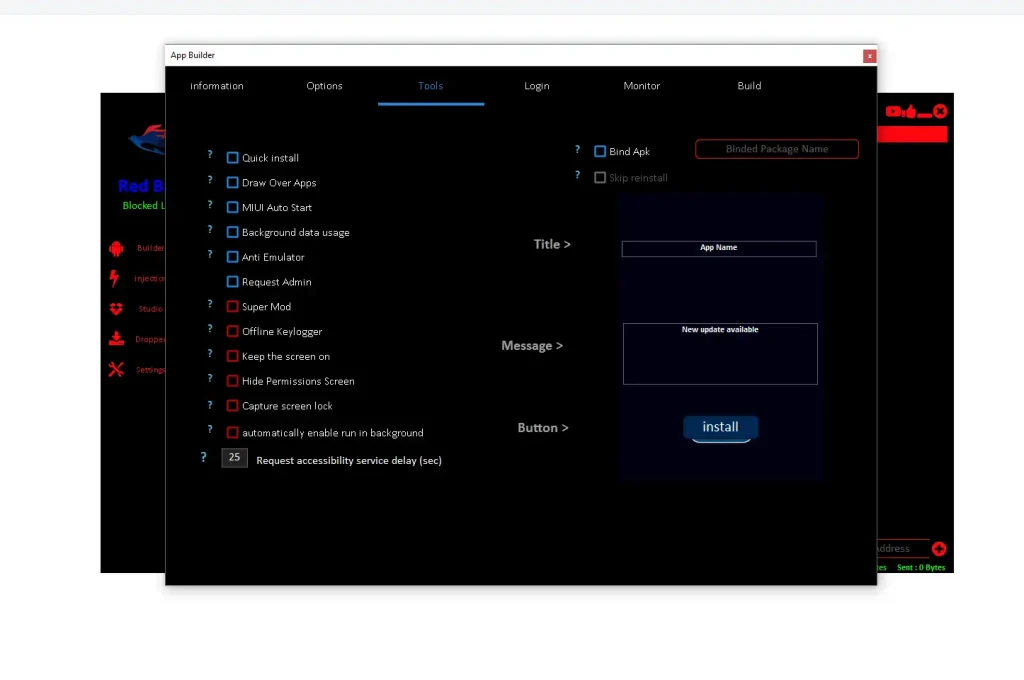
- 🪟 Overlay Attacks (UI Redressing):
RedBat RAT 2026 uses overlay permissions to display fake interfaces over legitimate apps, a technique known as UI redressing or tapjacking. This allows attackers to capture sensitive input such as banking credentials. It is one of the most effective mobile attack techniques. - 🧪 Sandbox & Emulator Detection (Anti-Analysis):
The malware detects virtual environments used for analysis and disables malicious behavior to avoid detection. This is a hallmark of advanced malware evasion techniques used in modern cyber threats. - 🔒 Persistent Access (Privilege Retention):
By obtaining device admin rights, RedBat ensures long-term persistence. It can survive reboots and resist removal attempts, making it a high-risk persistent threat.
⚙️ builder – C2 Configuration & Payload Generation
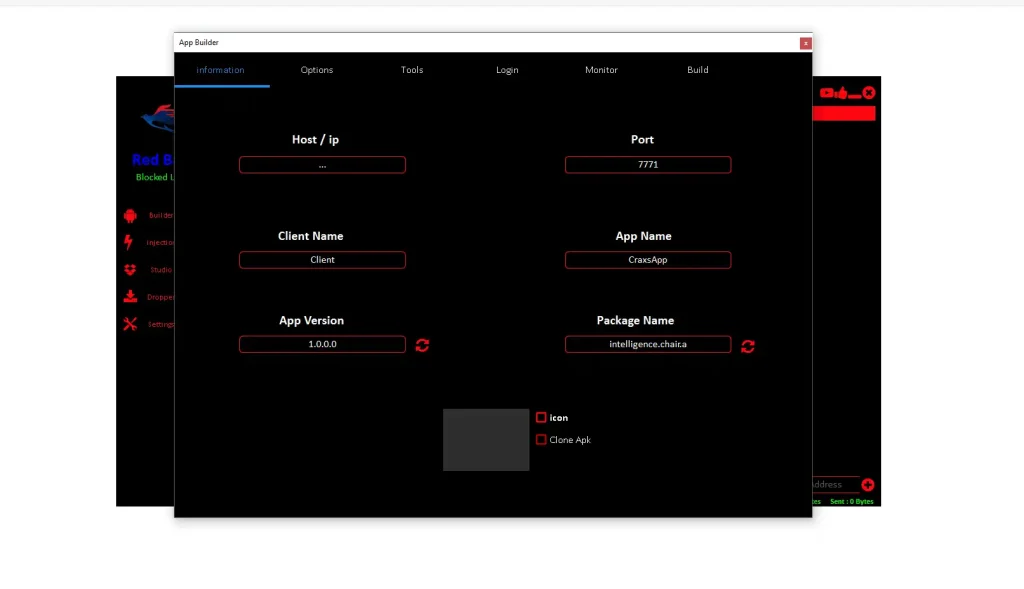
- 🌐 Command & Control Infrastructure (C2 Network):
RedBat RAT 2026 communicates with remote servers that issue commands and receive stolen data. This centralized system is known as a C2 infrastructure, a core component of modern malware operations. - 🔌 Non-Standard Port Usage (Network Evasion):
The malware uses uncommon ports to avoid detection by firewalls and intrusion detection systems. Monitoring unusual outbound traffic is critical for identifying such threats. - 🧾 Custom Payload Deployment (Targeted Attacks):
Attackers can generate customized payloads for specific targets, enabling targeted cyberattacks and campaign-based infections.
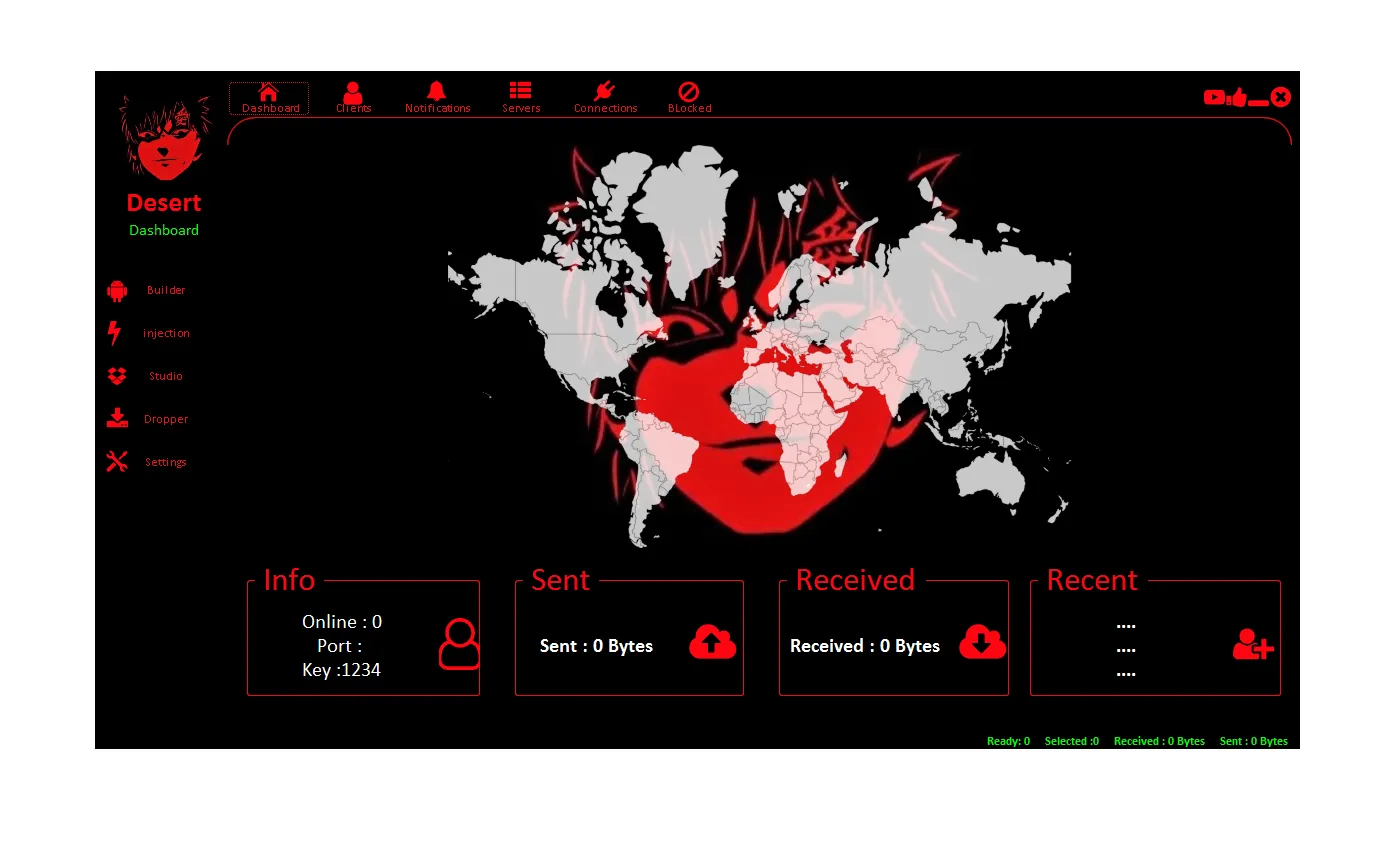
🖥️ client manager – Remote Control Dashboard
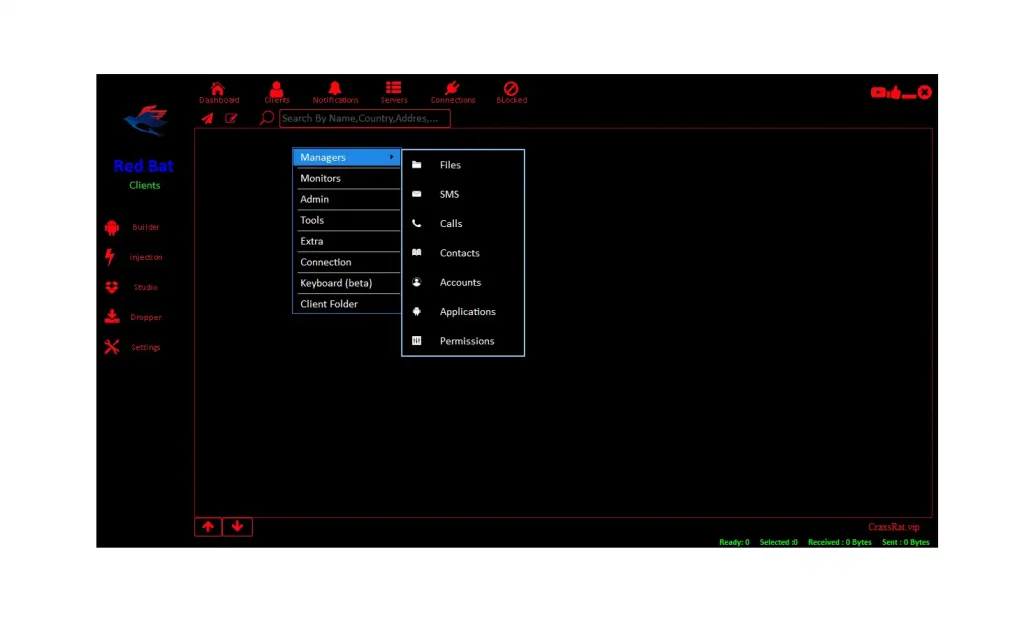
- 📊 Device Fleet Management (Botnet Control):
Attackers can manage multiple infected devices simultaneously, effectively creating a mobile botnet. This allows large-scale operations such as data theft and surveillance. - 📁 Full Data Access (Data Breach Risk):
The dashboard provides access to all device data, increasing the risk of large-scale data breaches and privacy violations. - 🌍 Global Attack Capability (Scalable Threat):
RedBat supports cross-region targeting, making it a global cybersecurity threat.
🎥 client monitor – Surveillance Arsenal
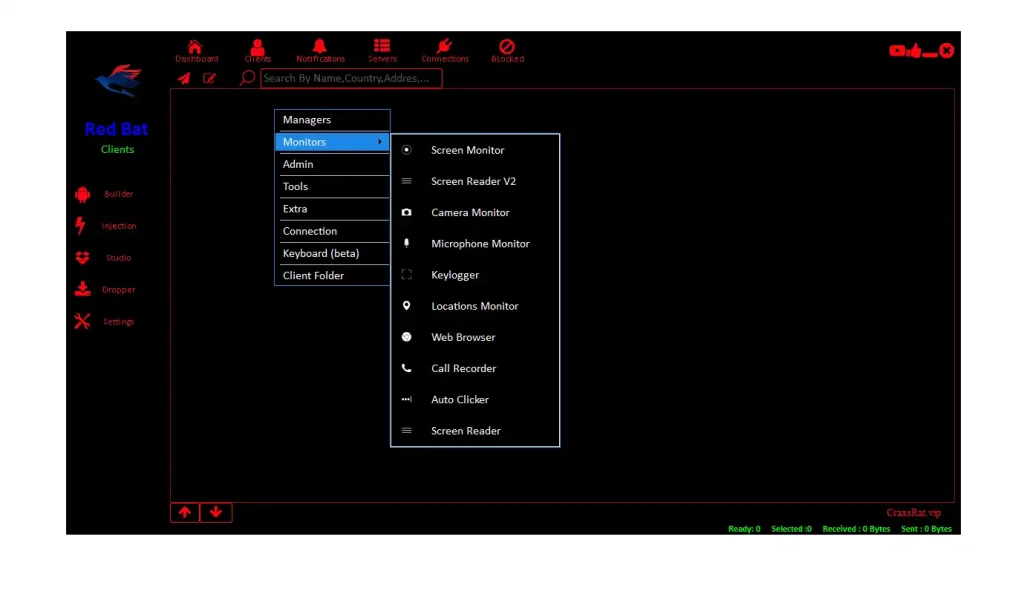
- 📷 Audio & Video Surveillance (Espionage):
Attackers can record audio and video, turning devices into surveillance tools. This is a serious privacy invasion and espionage risk. - 📍 Location Tracking (Geo Surveillance):
Real-time GPS tracking enables monitoring of user movements, often used in targeted attacks and stalking scenarios. - ⌨️ Keylogging (Sensitive Data Capture):
Captures all typed input, including passwords and financial data, making it a critical data theft mechanism.
⚡ client tools – Active Attack Tools
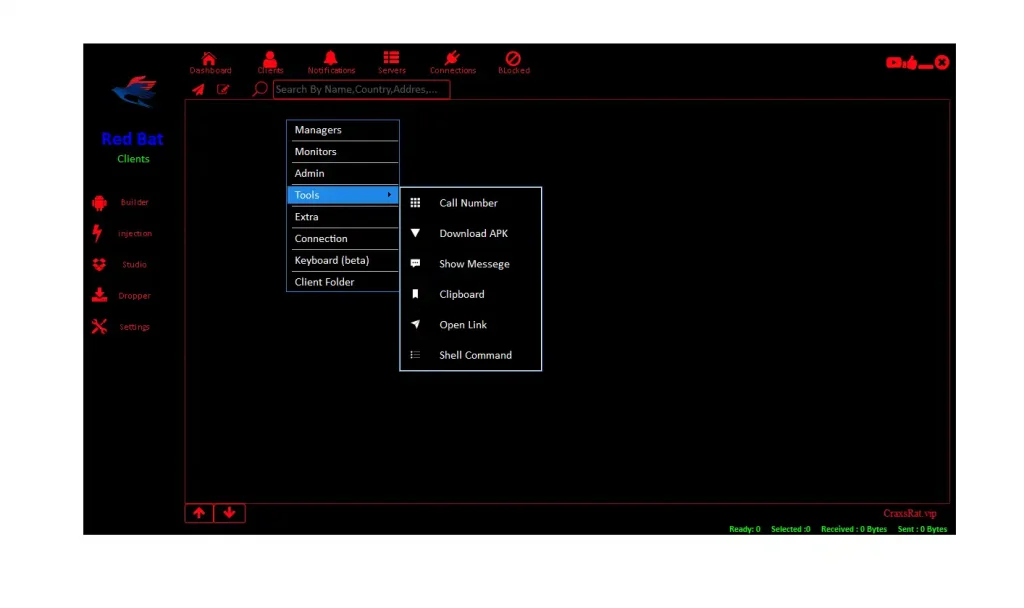
- 📥 Secondary Payload Deployment (Malware Expansion):
Allows installation of additional malware, increasing attack complexity. - 🌐 Forced Navigation (Phishing Automation):
Redirects users to malicious websites automatically. - 🖥️ Remote Command Execution (Full Control):
Enables attackers to execute commands, achieving complete device compromise.
📊 feature – Command & Control (C2) Dashboard
- 📊 Real-Time Monitoring (Threat Visibility):
Displays live status of infected devices. - 🔑 Centralized Operations (Attack Coordination):
Enables coordinated cyberattacks from a single interface. - 🔓 Weak Encryption (Security Flaw):
Weak keys can be exploited for malware analysis.
🧩 injection option – Payload Injection Settings
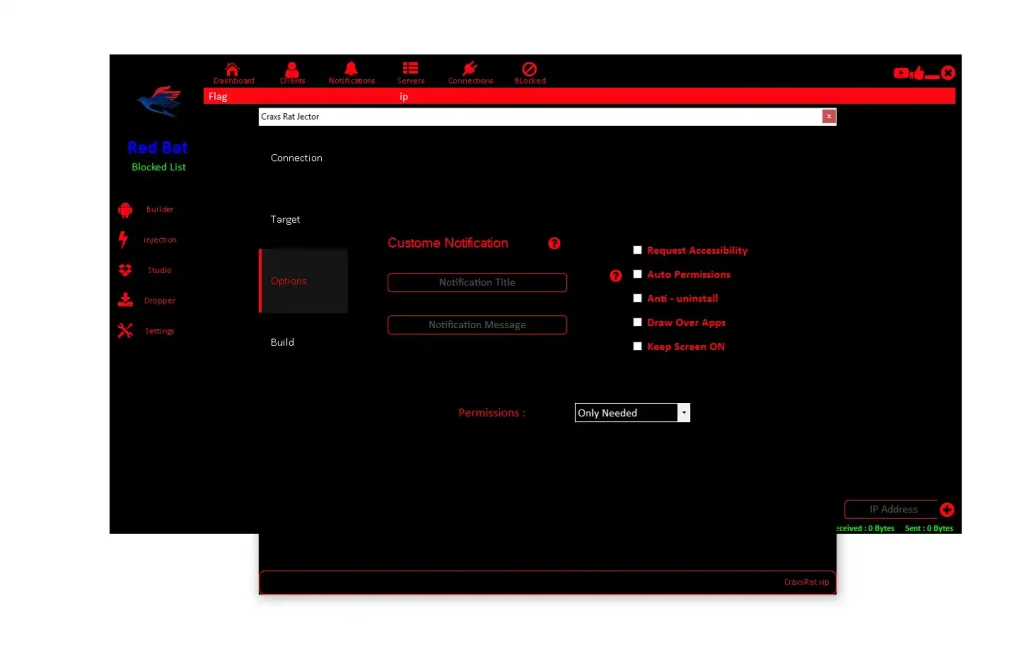
- 🔐 Permission Automation (Silent Access):
Grants permissions without user awareness. - 🛡️ Anti-Uninstall (Persistence):
Prevents removal of malware. - 🪟 Overlay Enablement (Phishing Support):
Supports UI-based attacks.
🎯 injection target – APK Targeting & Protection Bypass
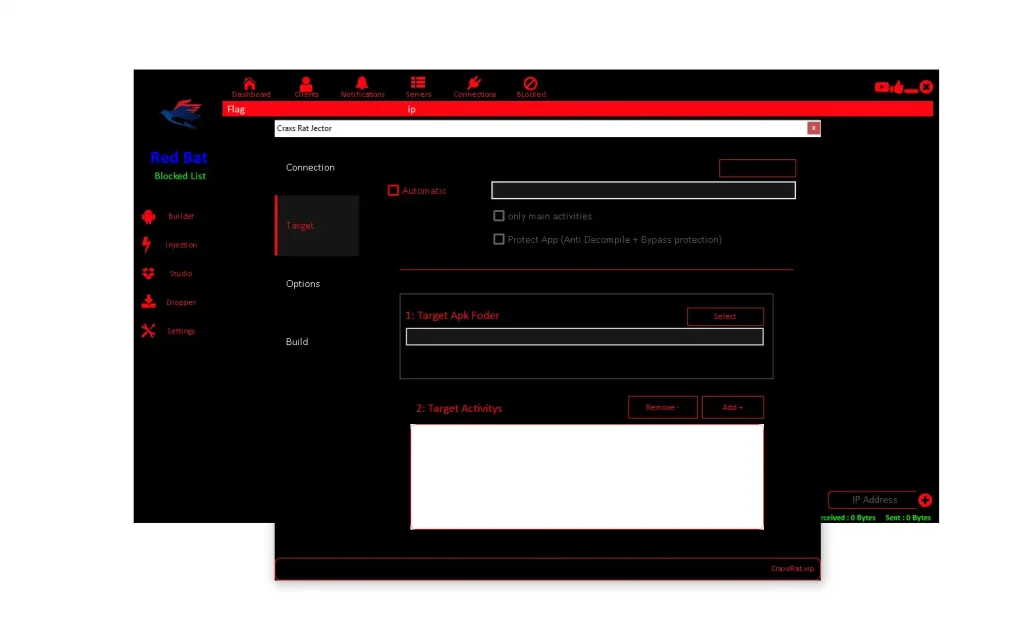
- 📂 Selective Injection (Stealth Attack):
Targets specific app components. - 🧪 Normal Functionality Preservation:
Keeps app working normally. - 🔍 Detection Avoidance:
Bypasses security tools.
⚙️ injection – Core Injection Configuration
- 🌐 C2 Setup:
Defines attacker communication. - 🔑 Encryption Handling:
Secures data transfer. - 🔌 Network Configuration:
Controls communication channels.
🔒 client previlage – Admin Rights Escalation
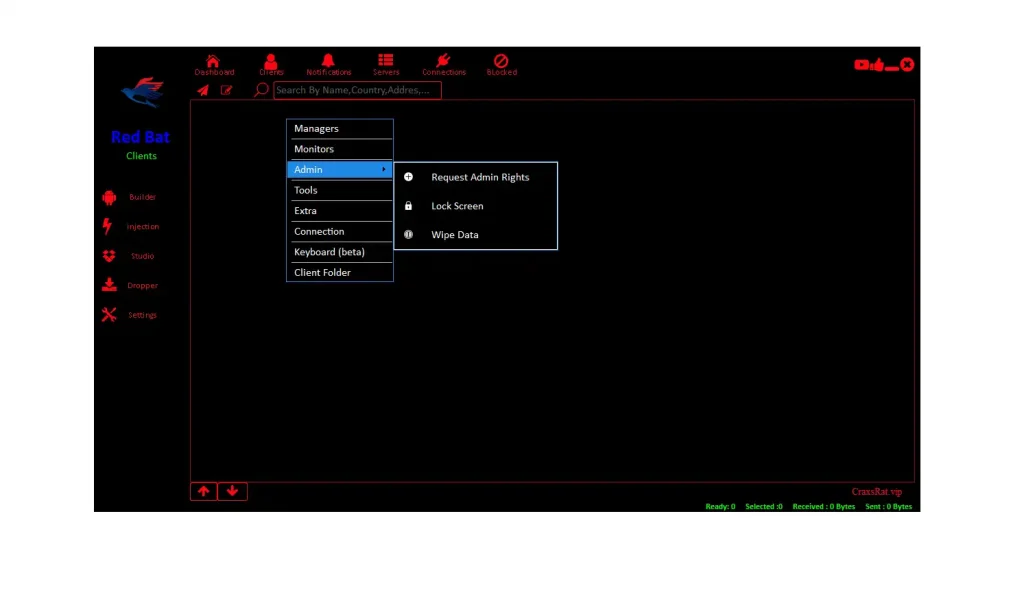
- 🛑 Full System Control:
Enables complete device takeover. - 🔐 Security Bypass:
Disables protections. - ❌ Persistent Infection:
Requires factory reset in severe cases.
🛡️ Detection & Mitigation Guide (2026)
🔍 Indicators of Compromise (IOCs)
- ⚠️ Abnormal permissions
- 📶 Suspicious traffic
- 🔋 Battery drain
✅ Protective Measures
- 🔐 Use trusted app sources
- 📱 Install mobile security tools
- 🔍 Monitor permissions
🚑 If Infected
- 🔄 Safe mode
- ❌ Remove apps
- 🔑 Change credentials
Download RedBat RAT 2026
Download RedBat RAT 2026 Link 1
Download RedBat RAT 2026 Link 2
Download RedBat RAT 2026 Link 3
🧾 Conclusion
RedBat RAT 2026 Android malware represents a next-generation mobile cyber threat, combining RAT capabilities, spyware behavior, and advanced evasion techniques. Its modular design, strong persistence, and data exfiltration features make it a major concern for both individuals and enterprises.
However, with proper cybersecurity awareness, mobile threat detection, and proactive defense strategies, users can effectively minimize risks and protect their digital assets.
❓ FAQs
❓ What is RedBat RAT 2026 Android malware?
It is an advanced remote access trojan that allows attackers to control Android devices and steal sensitive data.
❓ How does RedBat RAT 2026 spread?
It spreads through malicious APK files, often disguised as legitimate apps.
❓ What makes it dangerous?
Its ability to steal data, monitor users, and maintain persistent access makes it highly dangerous.
❓ Can antivirus detect it?
Advanced security tools can detect it, especially those using behavioral analysis.
❓ How can I stay protected?
Avoid unknown apps, monitor permissions, and use mobile security solutions.
❓ Is it a global threat?
Yes, it targets users worldwide, especially in regions with high smartphone usage.